A new ransomware group called Codefinger has developed an innovative attack method targeting Amazon Web Services (AWS) cloud storage, security researchers at Halcyon revealed this week.
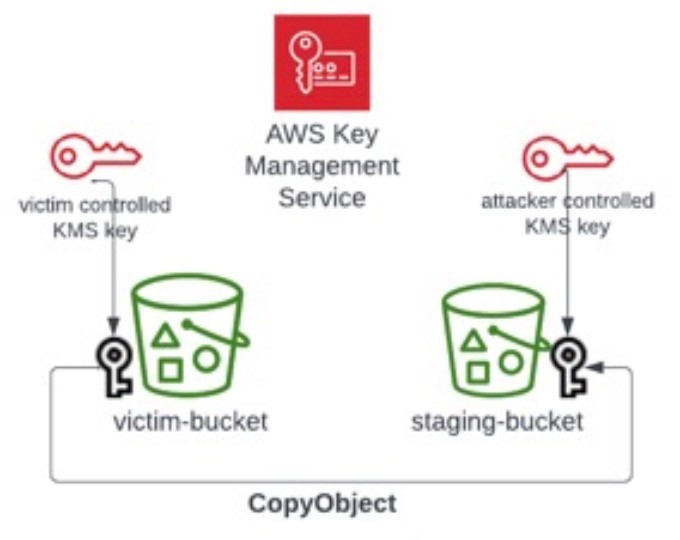
Unlike traditional ransomware that encrypts files locally, Codefinger exploits AWS's own Server-Side Encryption with Customer Provided Keys (SSE-C) feature to lock down victims' data stored in S3 buckets. The attack doesn't rely on any AWS vulnerabilities but instead uses stolen account credentials.
"Once encrypted, recovery is impossible without the attacker's key," explained Tim West, VP of Services at Halcyon RISE Team. The attackers retain the AES-256 encryption keys, while AWS only stores a hash that cannot be used for recovery.
To pressure victims into paying, Codefinger marks the encrypted files for deletion within seven days using AWS's native lifecycle policies. The group leaves ransom notes demanding Bitcoin payments.
Researchers have identified two victims so far, both AWS native software developers. The attack represents a concerning trend as it leverages legitimate cloud features and leaves minimal forensic evidence.
AWS customers can protect themselves by:
- Restricting SSE-C usage through IAM policies
- Monitoring AWS credentials closely
- Implementing detailed logging of S3 operations
- Regularly reviewing and rotating access keys
- Using temporary security credentials via AWS Security Token Service
The discovery highlights growing risks around cloud storage security. Security experts warn that similar encryption features in other cloud platforms could be vulnerable to comparable attacks.
AWS emphasized their shared responsibility model for security and urged customers to follow security best practices, particularly around protecting access credentials which are often exposed through code repositories or phishing attacks.