The recent technical failure of the Rockstar2FA phishing toolkit has led to a notable rise in activity from an emerging threat called FlowerStorm, according to a new report from cybersecurity firm Sophos.
Rockstar2FA, a phishing-as-a-service platform targeting Microsoft 365 credentials and session cookies, experienced what appears to be an infrastructure collapse on November 11, 2024. The service's pages became unreachable due to technical issues rather than law enforcement action.
In the wake of Rockstar2FA's disruption, researchers observed increased activity from FlowerStorm, a similar phishing service operational since June 2024. Both platforms share notable characteristics in their phishing portal designs and backend credential harvesting methods, suggesting possible connections between the two operations.
The platforms employ sophisticated techniques, including Cloudflare Turnstile integration to filter out automated traffic. While similarities exist, researchers have not established definitive links between the services. The timing could indicate a strategic shift, leadership changes, or deliberate separation of operations.
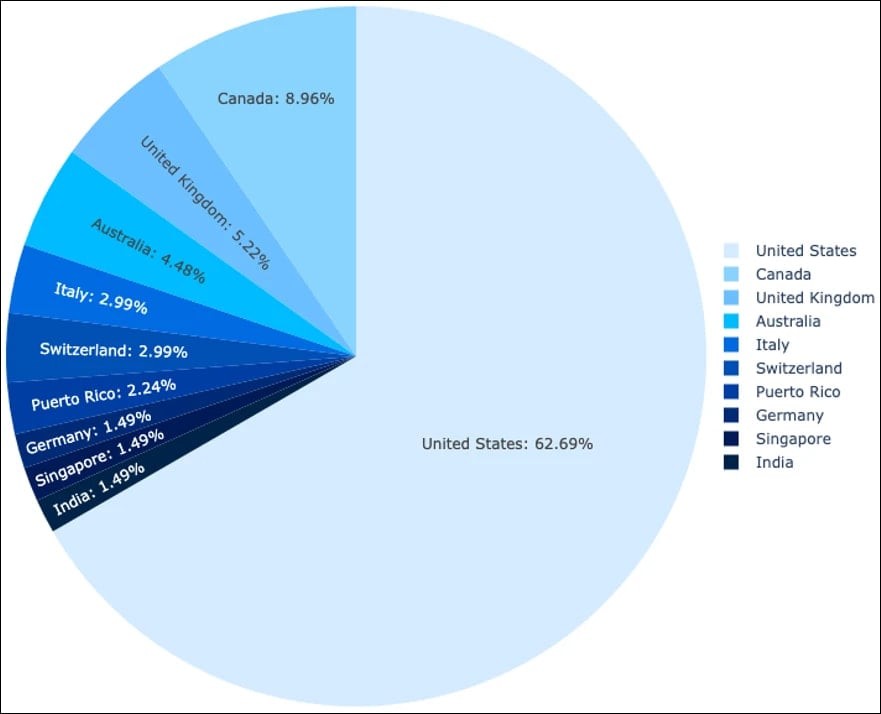
FlowerStorm primarily targets users in developed nations, with the United States, Canada, and the United Kingdom among the most affected. The service industry faces the heaviest impact, particularly engineering, construction, real estate, and legal services firms.
This development highlights a concerning trend in cybercrime, where readily available phishing toolkits enable threat actors to launch sophisticated attacks without extensive technical knowledge. The rapid transition of criminal activities from Rockstar2FA to FlowerStorm demonstrates the resilient nature of phishing-as-a-service operations.
Security experts recommend organizations strengthen their authentication measures and maintain vigilance against these evolving threats, particularly in the targeted sectors and regions.