Security researchers at Trend Micro have uncovered a deceptive GitHub repository distributing infostealer malware while posing as legitimate proof-of-concept (PoC) code for a recent Windows LDAP vulnerability.
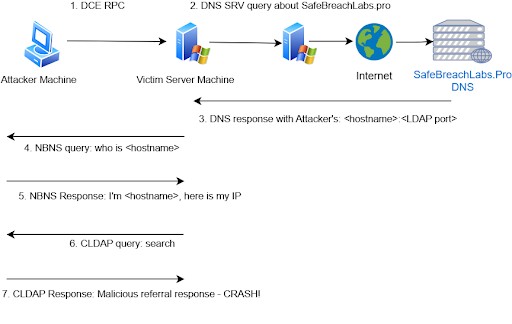
The malicious repository mimics SafeBreach Labs' authentic PoC for CVE-2024-49113, also known as LDAPNightmare - a denial-of-service vulnerability that Microsoft patched in December 2024.
When users download what appears to be the PoC exploit, they actually receive a UPX-packed executable that deploys a sophisticated multi-stage attack. The malware places a PowerShell script in the victim's temporary folder and creates a scheduled task that runs an encrypted script. This script then retrieves additional malicious code from Pastebin.
The final payload harvests sensitive system information including:
- Computer details
- Running processes
- Directory listings
- IP address and network data
- Installed updates
This collected data is compressed into a ZIP archive and exfiltrated to a remote FTP server using hardcoded credentials.
The attack exploits confusion around two separate LDAP vulnerabilities - CVE-2024-49113 and CVE-2024-49112. An initial misquote in SafeBreach's blog post generated heightened interest around LDAPNightmare, which the threat actors appear to have capitalized on.
Security experts warn that this tactic of disguising malware as security research tools is an ongoing threat. They recommend users exercise caution when downloading public exploits and verify the authenticity of repositories, particularly since attackers have been known to impersonate established security researchers.