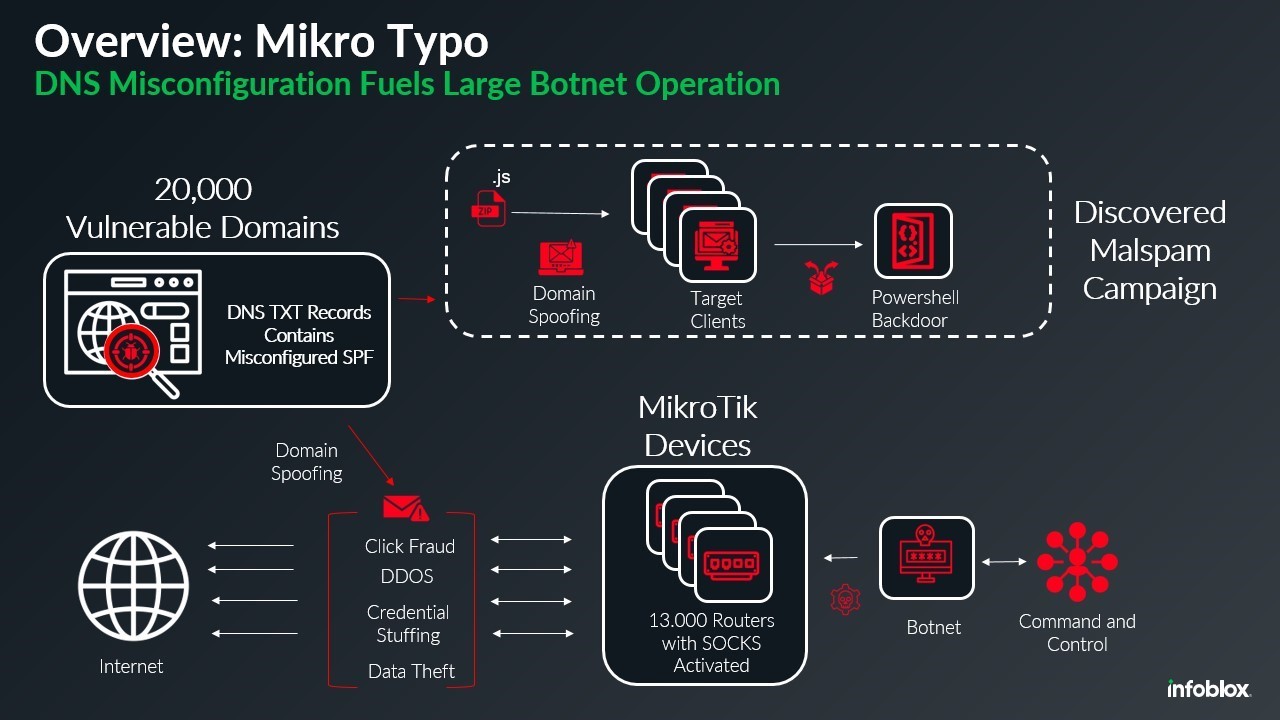
A massive botnet comprising 13,000 compromised MikroTik routers is actively exploiting DNS misconfigurations to bypass email security and distribute malware while spoofing approximately 20,000 domains.
Security researchers at Infoblox uncovered the botnet after detecting a malicious spam campaign in late November that impersonated DHL shipping notifications. The fraudulent emails contained zip file attachments labeled as invoices or tracking information, which delivered obfuscated malware through JavaScript files.
Analysis revealed the botnet consists of hijacked MikroTik routers running various firmware versions. The compromised devices are being used as SOCKS proxies, allowing attackers to mask their origin and enabling unauthorized access to the network.
"The botnet operators are exploiting improperly configured DNS records related to the Sender Policy Framework (SPF), which normally controls which servers can send emails for specific domains," explained the research team.
The misconfiguration allows any server to send emails appearing to come from legitimate domains. This could be accidental or potentially caused by unauthorized access to domain registrar accounts.
The malware delivered through this campaign connects to command-and-control infrastructure previously associated with Russian cyber activity. Given the botnet's size, it can be leveraged for various attacks including:
- Distributed denial-of-service (DDoS) attacks
- Large-scale phishing campaigns
- Malware distribution
- Command-and-control operations
Security experts recommend organizations regularly audit their DNS configurations and SPF records to prevent exploitation. Proper SPF setup should explicitly specify authorized email servers and deny access to all others.
The discovery highlights ongoing security challenges with IoT devices and the importance of proper network security controls to prevent devices from being conscripted into botnets.