A new wave of cyberattacks targeting Juniper Networks' Session Smart Router (SSR) devices has been detected, with the notorious Mirai botnet exploiting systems using default passwords.
Multiple customers reported suspicious activities on their Session Smart Network (SSN) platforms on December 11, 2024. According to Juniper Networks, compromised devices were subsequently used to launch distributed denial-of-service attacks against other network-accessible systems.
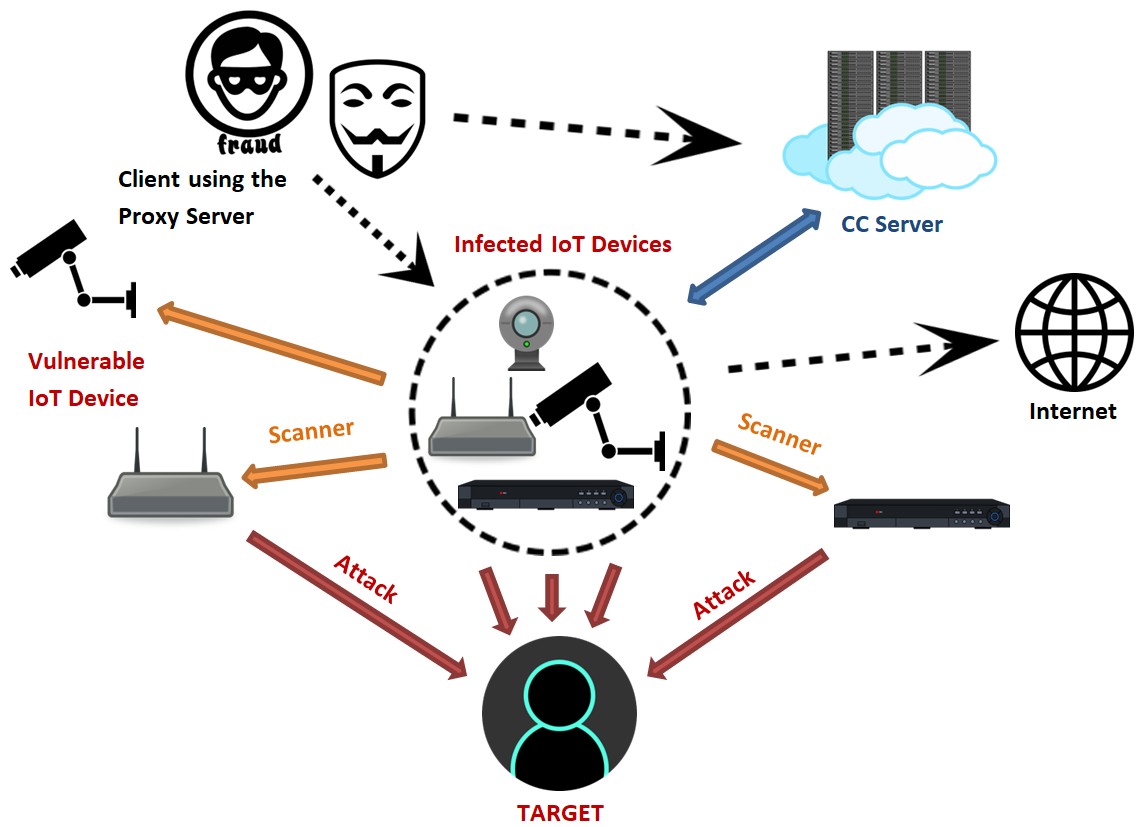
The Mirai malware specifically targets devices with factory-default credentials, allowing attackers to execute remote commands through SSH attacks. Common indicators of Mirai infection include unusual port scanning activity, multiple failed SSH login attempts, unexpected spikes in outbound traffic, and erratic device behavior.
In response to these attacks, Juniper Networks has issued several security recommendations for SSR users:
- Change default passwords immediately and implement strong authentication
- Monitor access logs regularly for suspicious activities
- Deploy firewalls and intrusion detection systems
- Keep device firmware updated with latest patches
The company emphasizes that all affected systems were using default passwords, highlighting the importance of basic security hygiene in preventing such compromises.
This latest Mirai campaign demonstrates the ongoing threat posed by IoT-targeting botnets, particularly against devices with weak security configurations. Network administrators are advised to take immediate action to secure their SSR deployments against these attacks.
#cybersecurity #networking #security