A sophisticated new malware called "Fickle Stealer" has emerged, using multiple distribution methods and advanced targeting capabilities. The Rust-based stealer was discovered by security researchers in May 2024.
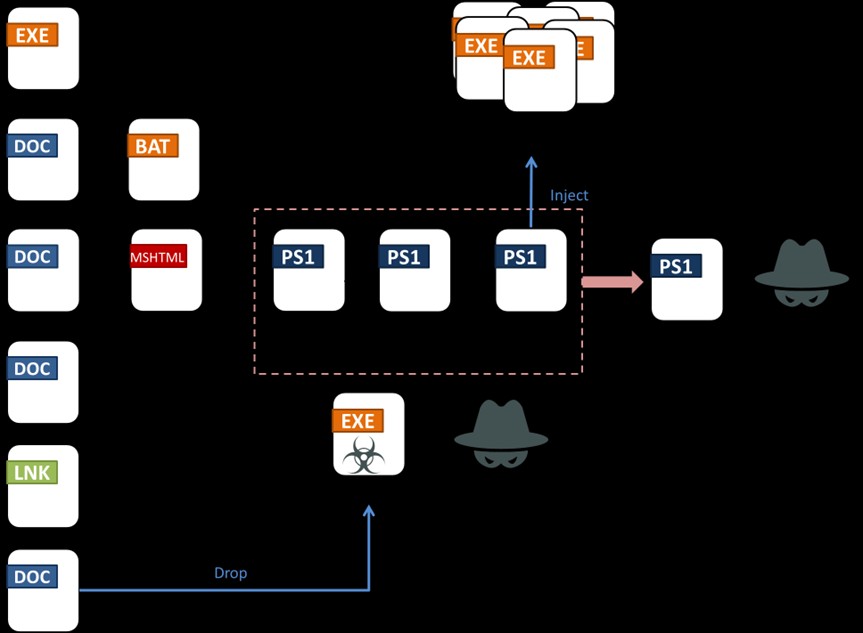
The malware employs four main delivery methods to infect systems:
- VBA dropper using Word documents
- VBA downloader through Word files
- Direct link downloads
- Executable downloader masquerading as PDF viewer
Once delivered, Fickle Stealer performs preparatory work including bypassing User Account Control (UAC) and establishing persistence. It uses techniques like fake management console files and mock trusted directories to evade detection.
The malware includes sophisticated anti-analysis capabilities, checking for:
- Debugging tools
- Virtual machine environments
- Analysis software
- Suspicious usernames
- Known sandbox hardware IDs
After passing these checks, Fickle Stealer communicates with command servers to receive targeting instructions. It then systematically steals data from:
- Cryptocurrency wallets
- Browser data
- Password managers
- Gaming platforms
- Communication apps
- Documents and files
The stolen information is compressed, encrypted and exfiltrated in a specialized JSON format. The malware's modular nature allows its operators to dynamically update target lists and adapt its behavior.
According to researchers, ongoing development and frequent updates to attack chains indicate this is an active threat requiring continued monitoring. The malware's use of Rust programming makes analysis more challenging due to complex assembly code.
Organizations are advised to maintain security controls and monitor for signs of compromise, as Fickle Stealer represents an evolving data theft threat.