A sophisticated malware campaign targeting Czech bank customers has been uncovered by security researchers at ESET. The malware, dubbed NGate, uses a novel technique to steal money by relaying NFC payment card data through victims' Android phones to attackers' devices.
The campaign operated in the Czech Republic from November 2023 until March 2024, when authorities arrested a 22-year-old suspect carrying over $6,500 in stolen cash.
How the Attack Works
The attackers first send SMS messages to random phone numbers, claiming recipients are eligible for tax refunds. Victims who click the link download a malicious app impersonating their bank.
After capturing banking credentials, attackers call victims pretending to be bank security, warning their account was compromised. They then convince victims to install the NGate malware, presented as a security tool.
The malware prompts victims to:
- Enter banking details and card PIN
- Enable NFC on their phone
- Place their payment card against the phone
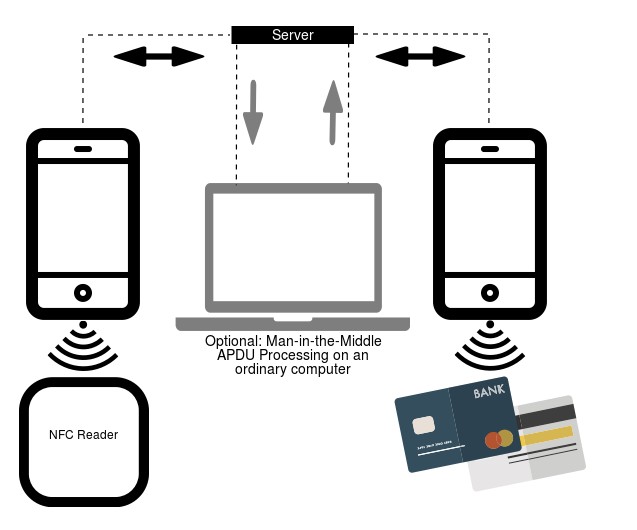
Behind the scenes, NGate relays the card's NFC data to the attacker's rooted Android device, which can then clone the card for ATM withdrawals.
Technical Details
NGate is based on NFCGate, an open-source tool developed by German university students for analyzing NFC traffic. The malware specifically misuses NFCGate's relay capabilities to transmit card data.
The malware displays phishing pages through WebView and uses JavaScript interfaces to:
- Check device NFC status
- Set up relay servers
- Initiate NFC data capture
Protection Measures
To avoid falling victim to NGate and similar threats:
- Only install apps from the Google Play Store
- Be wary of unsolicited SMS messages about refunds
- Keep payment card PINs confidential
- Use mobile security apps
- Disable NFC when not in use
- Consider using digital wallet apps instead of physical cards
While currently focused on Czech banks, security researchers warn the attack method could spread to other regions.