Russian state-sponsored hacking group APT29 has launched a sophisticated cyber espionage campaign using malicious Remote Desktop Protocol (RDP) attacks against high-profile targets worldwide.
The campaign, detected in October 2024, primarily targeted government agencies, think tanks, academic researchers, and Ukrainian organizations. The attackers repurposed legitimate red teaming methodologies to compromise victim systems through carefully crafted spear-phishing emails.
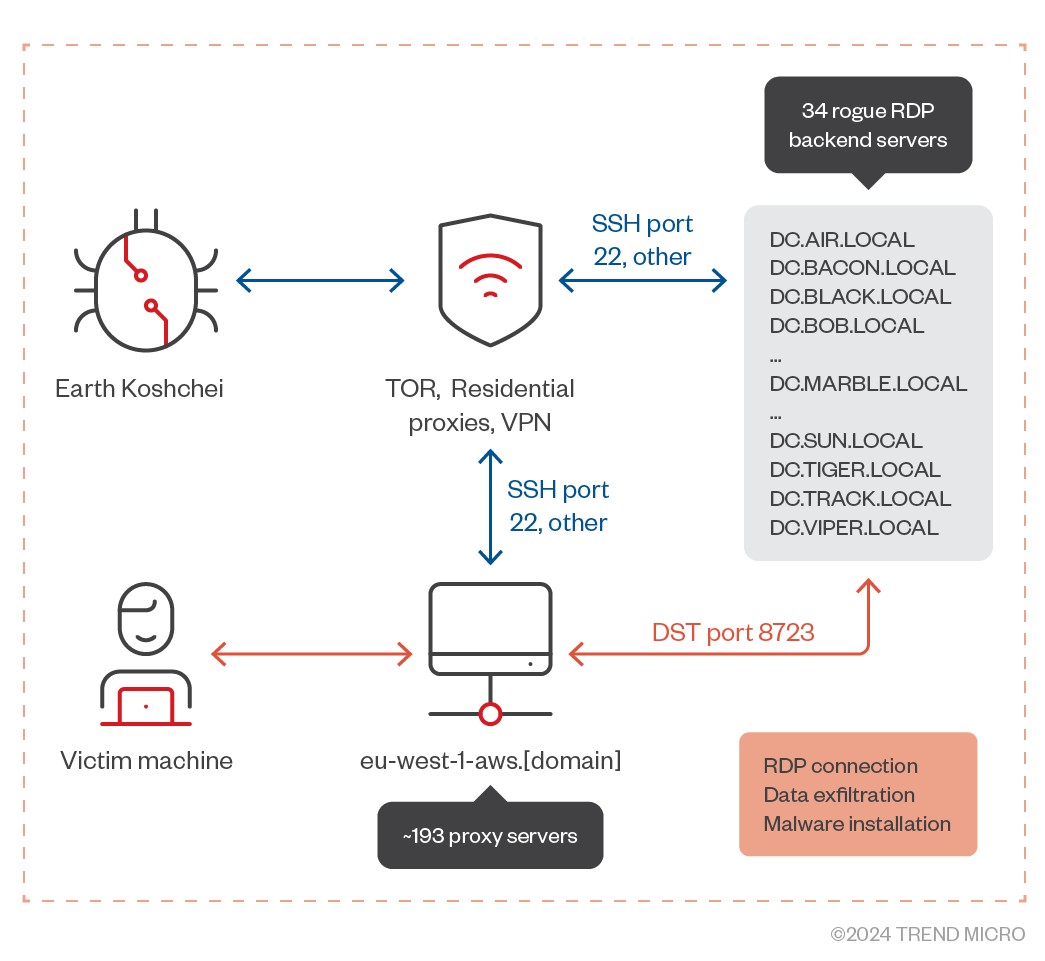
According to research by Trend Micro, APT29 (also known as Earth Koshchei and Cozy Bear) sent malicious RDP configuration files to victims. When opened, these files connected the target's machine to one of 193 RDP relay servers controlled by the group.
The attack campaign showed extensive preparation, with domain registrations beginning in August 2024 targeting Australian and Ukrainian government-linked entities. In a single day in October, the group targeted approximately 200 high-profile victims.
The hackers leveraged PyRDP, an open-source tool typically used by security researchers, to intercept and manipulate RDP connections. This allowed them to automatically collect data from shared drives and save contents locally on attacker-controlled systems.
To evade detection, APT29 employed multiple layers of anonymization, including:
- TOR exit nodes
- Over 200 VPS IP addresses
- 34 rogue RDP servers
- Commercial VPN services
- Residential proxy providers
The attack technique proved particularly stealthy as it did not require deploying custom malware. Instead, the group used malicious configuration files to facilitate data collection and system access.
Upon successful connection, the rogue server would execute a remote application disguised as "AWS Secure Storage Connection Stability Test" while redirecting local drives, printers, COM ports, smart cards, and clipboards - giving attackers broad access to victim machines.
Security experts note this campaign demonstrates APT29's continued evolution in adopting new attack methodologies, particularly their ability to repurpose legitimate security testing tools for malicious purposes.