Russian-linked threat actors have launched a sophisticated phishing campaign targeting Microsoft 365 accounts through an advanced technique called device code authentication phishing. The attacks have impacted government agencies, NGOs, defense organizations, and private companies across multiple continents.
Microsoft Threat Intelligence has identified a group known as Storm-2372 conducting these operations since August 2024. The attackers pose as users of popular messaging apps like WhatsApp and Microsoft Teams, sending fake meeting invitations that lead victims to legitimate Microsoft login pages where they unknowingly authenticate malicious sessions.
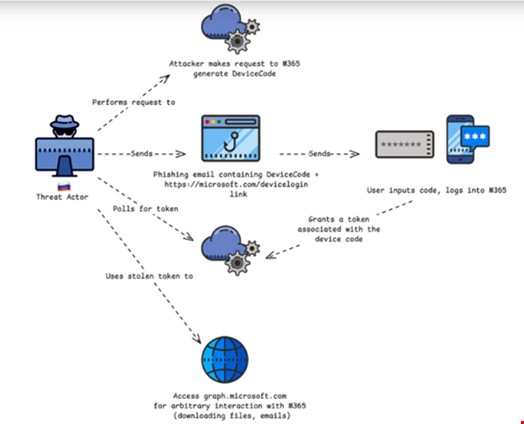
The attack exploits device code authentication - a legitimate Microsoft feature designed for logging into services from devices without web browsers. Attackers generate a device code and use targeted social engineering to trick victims into entering it on Microsoft's sign-in page. This gives attackers control of the account without needing passwords or bypassing multi-factor authentication.
According to cybersecurity firm Volexity, at least three Russian threat groups - CozyLarch (APT29), UTA0304, and UTA0307 - have employed this technique since early 2025. The groups frequently impersonate government officials and diplomatic entities, including the U.S. Department of State and European Parliament, to target victims.
Each group uses distinct tactics:
- UTA0304 created a fake secure chat platform
- CozyLarch sent fraudulent U.S. State Department Teams meeting invites
- UTA0307 built a deceptive Microsoft login page generating real device codes
Once attackers gain access, they search for sensitive data, send additional phishing emails internally, and steal emails and cloud documents. The method leaves minimal security traces, making detection challenging.
Microsoft has begun alerting targeted users and monitoring for suspicious authentication attempts as part of ongoing mitigation efforts. Organizations are advised to remain vigilant against these sophisticated social engineering attacks targeting their Microsoft 365 environments.