Critical 'AirBorne' Vulnerabilities Allow Remote Hijacking of Apple AirPlay Devices
Researchers discovered severe security flaws in Apple's AirPlay technology that enable zero-click remote attacks on millions of devices. The 'AirBorne' vulnerabilities could let attackers take control of smart speakers and TVs without user interaction, highlighting major security risks in connected home devices.
CISA Extends Critical CVE Program Funding in Last-Minute Decision
CISA has granted an 11-month extension to MITRE for managing the globally essential CVE vulnerability database, averting a potential crisis just hours before contract expiration. The incident has sparked discussions about establishing a CVE Foundation to ensure long-term stability through a non-profit model.
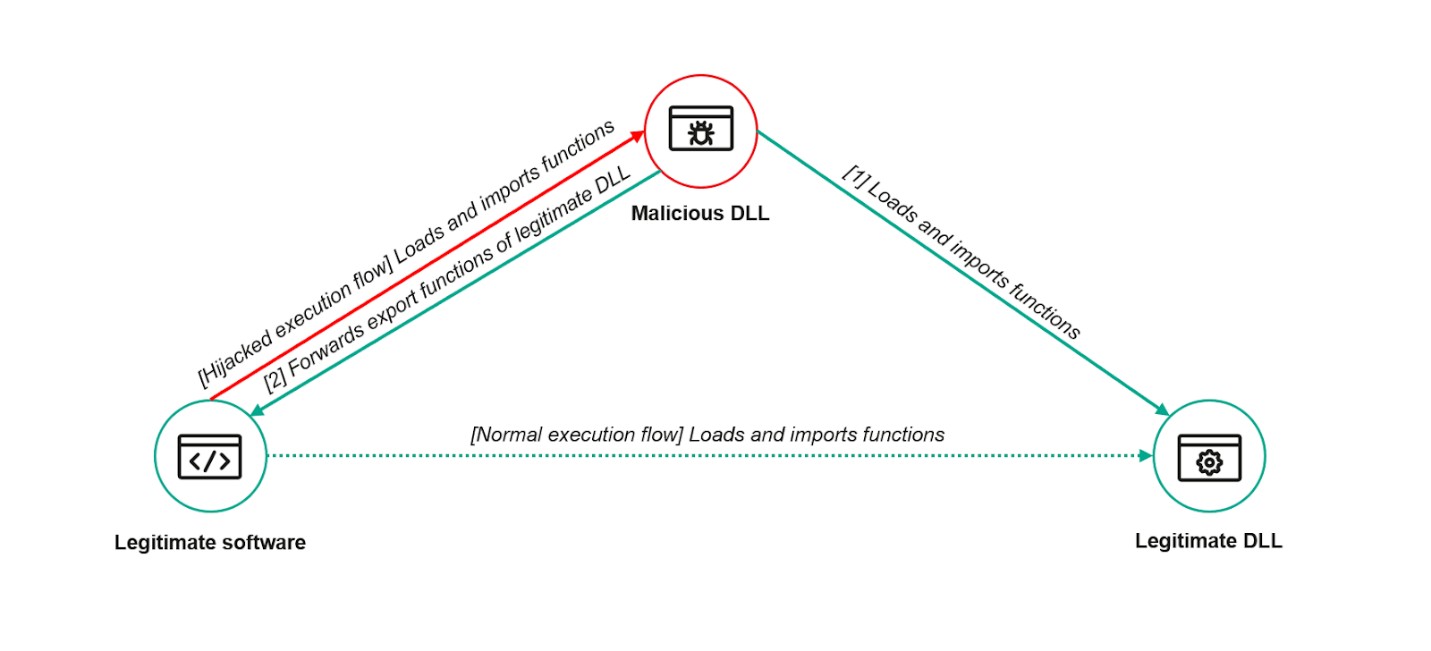
ToddyCat Hackers Exploit ESET Antivirus Flaw to Deploy Stealthy TCESB Malware
A sophisticated hacking group called ToddyCat successfully exploited a vulnerability in ESET's antivirus software to secretly install advanced malware. The attack leveraged DLL Search Order Hijacking to deploy TCESB, a stealthy C++ tool designed to evade security monitoring.
Critical RCE Flaw in CentreStack File Sharing Platform Actively Exploited in the Wild
A severe vulnerability in CentreStack's file-sharing platform enables attackers to execute unauthorized code through hardcoded security keys. The actively exploited flaw affects both CentreStack and Triofox enterprise solutions, with patches now available from developer Gladinet.
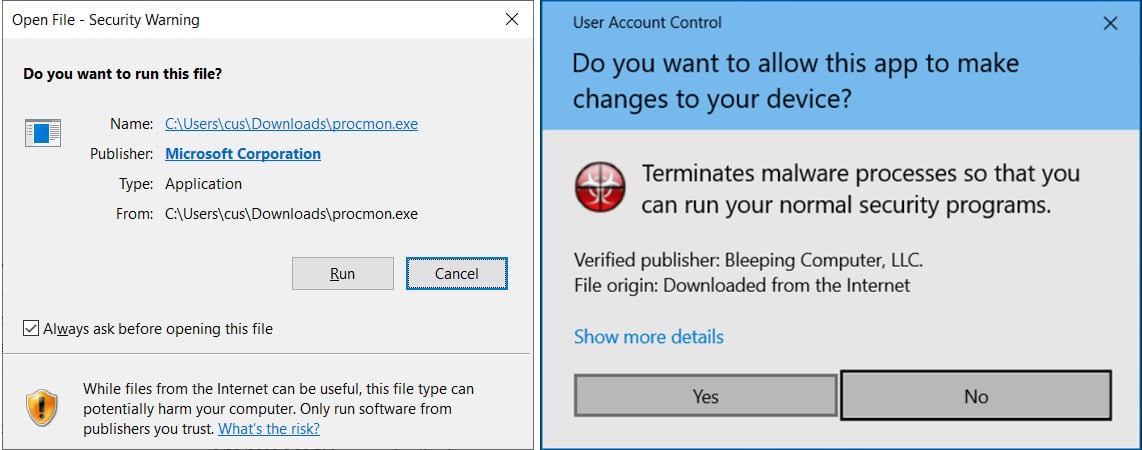
Critical WhatsApp Windows Flaw Could Let Attackers Disguise Malware as Innocent Files
A dangerous security vulnerability in WhatsApp's Windows client enables attackers to mask malware as harmless file attachments due to inconsistent MIME type handling. Meta urges users to immediately update to version 2.2450.6 or later to protect against potential malware attacks.
Critical WinRAR Vulnerability Evades Windows Security Protections
A newly discovered WinRAR security flaw allows attackers to bypass Windows' Mark of the Web security feature, potentially exposing users to malware. Microsoft has patched the high-severity vulnerability, which was being exploited through fake WinRAR websites distributing malicious software.
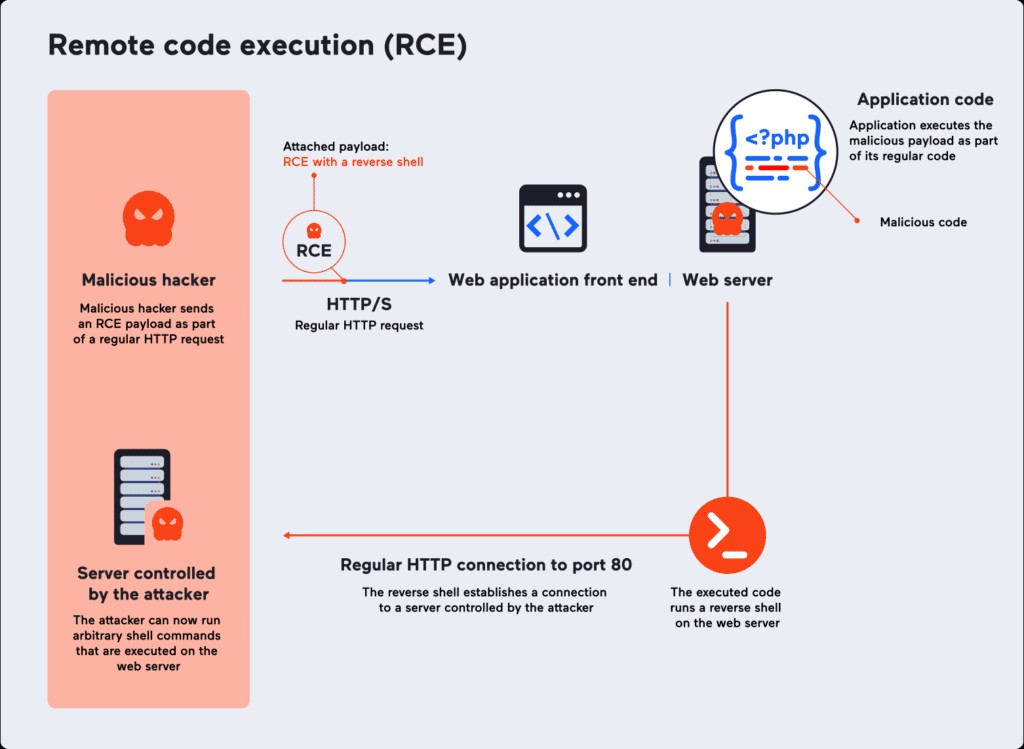
Critical Apache Parquet Vulnerability Exposes Systems to Remote Code Execution
A severe security flaw in Apache Parquet's Java Library enables attackers to execute arbitrary code through malicious files. The vulnerability, rated with maximum severity, affects all versions up to 1.15.0 and requires immediate patching to version 1.15.1.
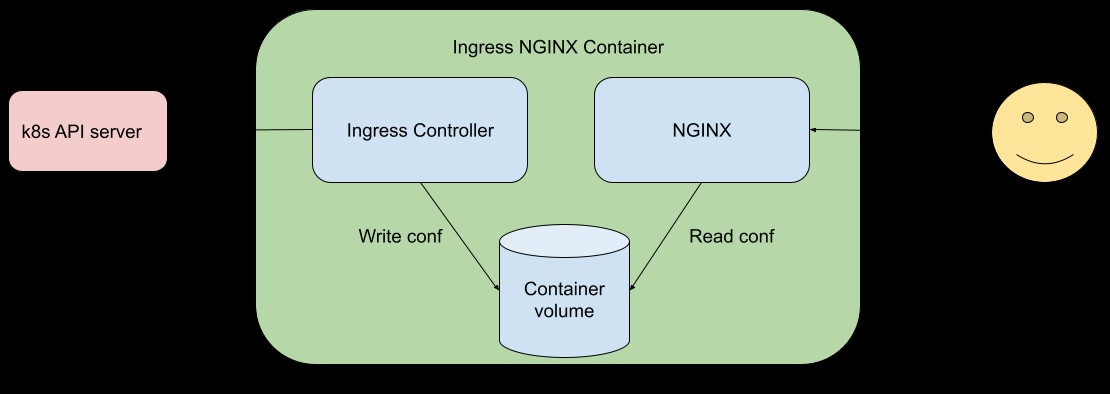
Critical RCE Vulnerability Exposes Thousands of Kubernetes Clusters to Attack
A severe set of security flaws dubbed 'IngressNightmare' threatens over 6,500 Kubernetes clusters using Ingress NGINX Controller. The vulnerabilities allow unauthenticated remote code execution with a critical CVSS score of 9.8, potentially enabling complete cluster takeover.
Critical Vulnerabilities in Fedora's Pagure Platform Expose Supply Chain Attack Risks
Security researchers discovered multiple critical vulnerabilities in Fedora's Pagure code hosting platform that could enable supply chain attacks through malicious code injection. The most severe flaw allowed attackers to compromise repositories and package specifications, leading Fedora to patch the issues and plan migration to Forgejo.
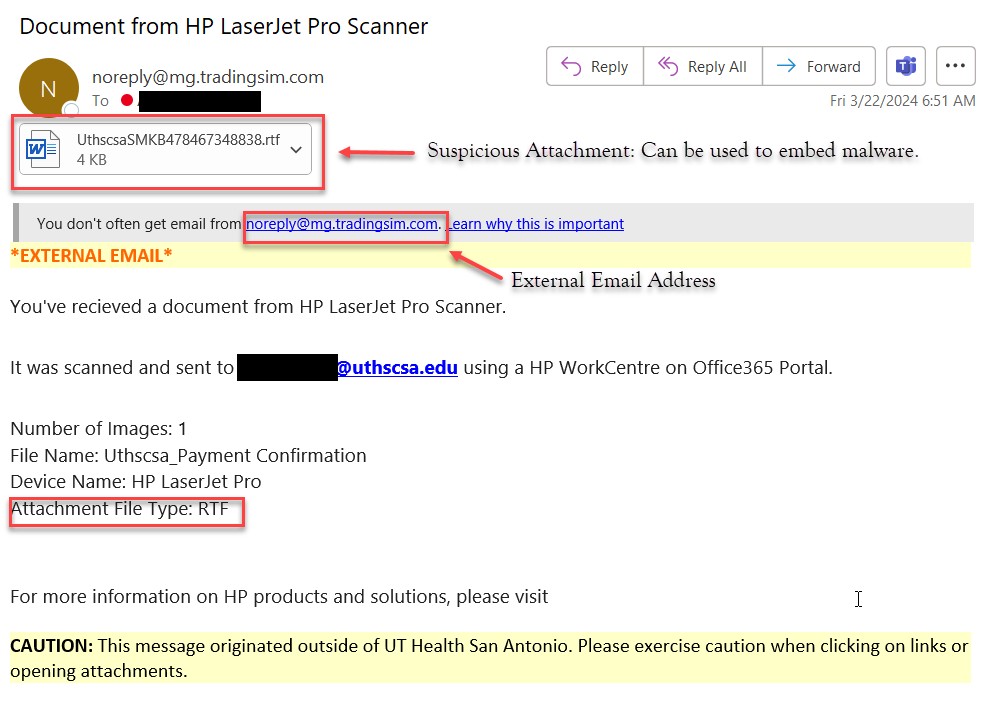
Critical HP Printer Vulnerability Puts Enterprise Networks at Risk Through Postscript Exploit
HP discloses severe security flaws affecting hundreds of LaserJet printer models, with a critical vulnerability enabling code execution through Postscript jobs. The company has released urgent firmware updates for approximately 120 printer series to address these high-risk security gaps.