xAI Security Breach Exposes Private API Key to SpaceX and Tesla Language Models
A critical security incident at Elon Musk's xAI revealed an API key that granted access to over 60 private LLMs containing sensitive SpaceX and Tesla data. The credentials remained exposed on GitHub for two months before the company's security team was alerted.
Cryptocurrency npm Packages Compromised in Nine-Year API Key Theft Campaign
Multiple long-standing npm packages were discovered to contain malicious code designed to steal API keys and sensitive data through obfuscated scripts. The attack targeted eleven packages including popular blockchain development libraries, with evidence pointing to compromised maintainer accounts.
AI-Generated Fake Security Reports Threaten Open-Source Software Community
Artificial intelligence tools are flooding open-source projects with false vulnerability reports and deceptive code contributions, overwhelming maintainers and potentially compromising security. The crisis has grown so severe that some projects have abandoned traditional vulnerability tracking systems while the community scrambles to implement stricter verification processes.
Stanford Researchers Create Powerful AI Model for Just $50, Challenging Industry Giants
Stanford and University of Washington researchers have developed an AI reasoning model for under $50 that rivals million-dollar systems. Using innovative distillation techniques and strategic training data selection, the s1 model demonstrates competitive performance while making AI research more accessible.
Critical Security Flaw: Go Module Mirror Served Malicious Package for Three Years
A major security breach in Google's Go Module Mirror exposed developers to a sophisticated backdoored package masquerading as a popular library for over three years. The malicious typosquatting attack potentially compromised thousands of development environments through remote command execution capabilities.
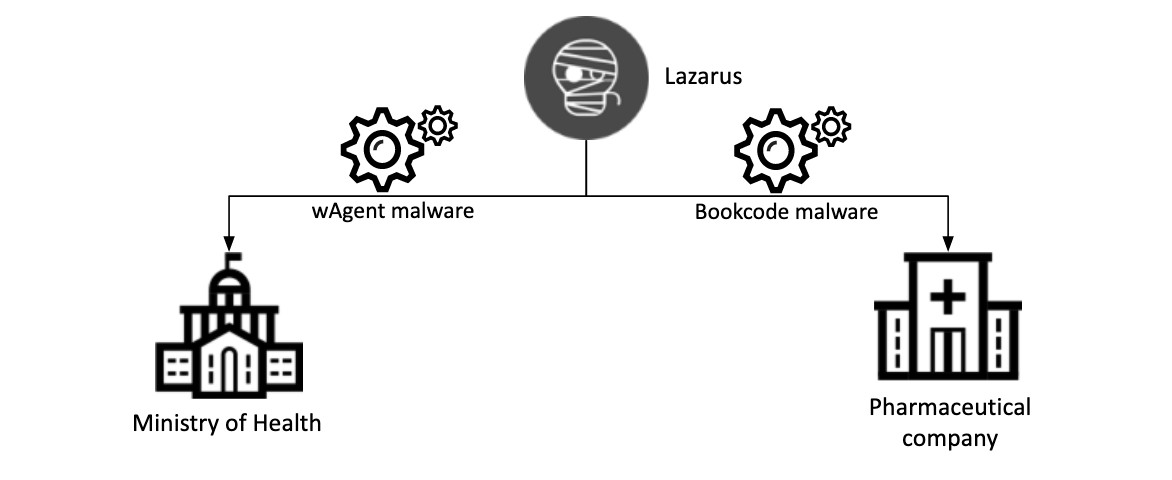
North Korean Hackers Deploy Hidden 'Phantom Circuit' to Control Global Cyber Operations
SecurityScorecard researchers uncover Lazarus group's sophisticated administrative layer used to manage cybercrime targeting cryptocurrency and software developers. The hidden infrastructure, linked to Pyongyang, oversees malware delivery and stolen data while exploiting LinkedIn recruitment schemes.
Malicious npm Packages Target Solana Users in Sophisticated Crypto Theft Campaign
Security researchers uncover a sophisticated attack using fake npm packages to steal Solana wallet credentials through Gmail's SMTP servers. The multi-platform campaign includes malicious GitHub repositories and packages with destructive capabilities, highlighting critical risks in the cryptocurrency software supply chain.
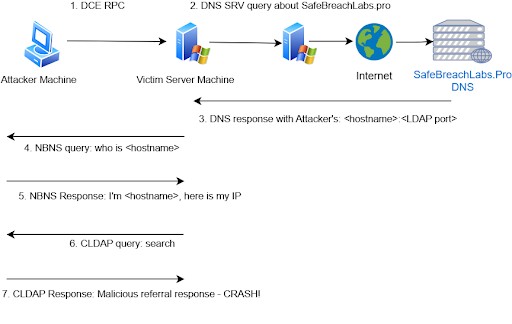
Malware Campaign Impersonates Windows LDAP Vulnerability Research
Security researchers have discovered a deceptive GitHub repository distributing infostealer malware while masquerading as proof-of-concept code for a Windows LDAP vulnerability. The sophisticated multi-stage attack harvests sensitive system data and exploits confusion around two separate LDAP vulnerabilities.
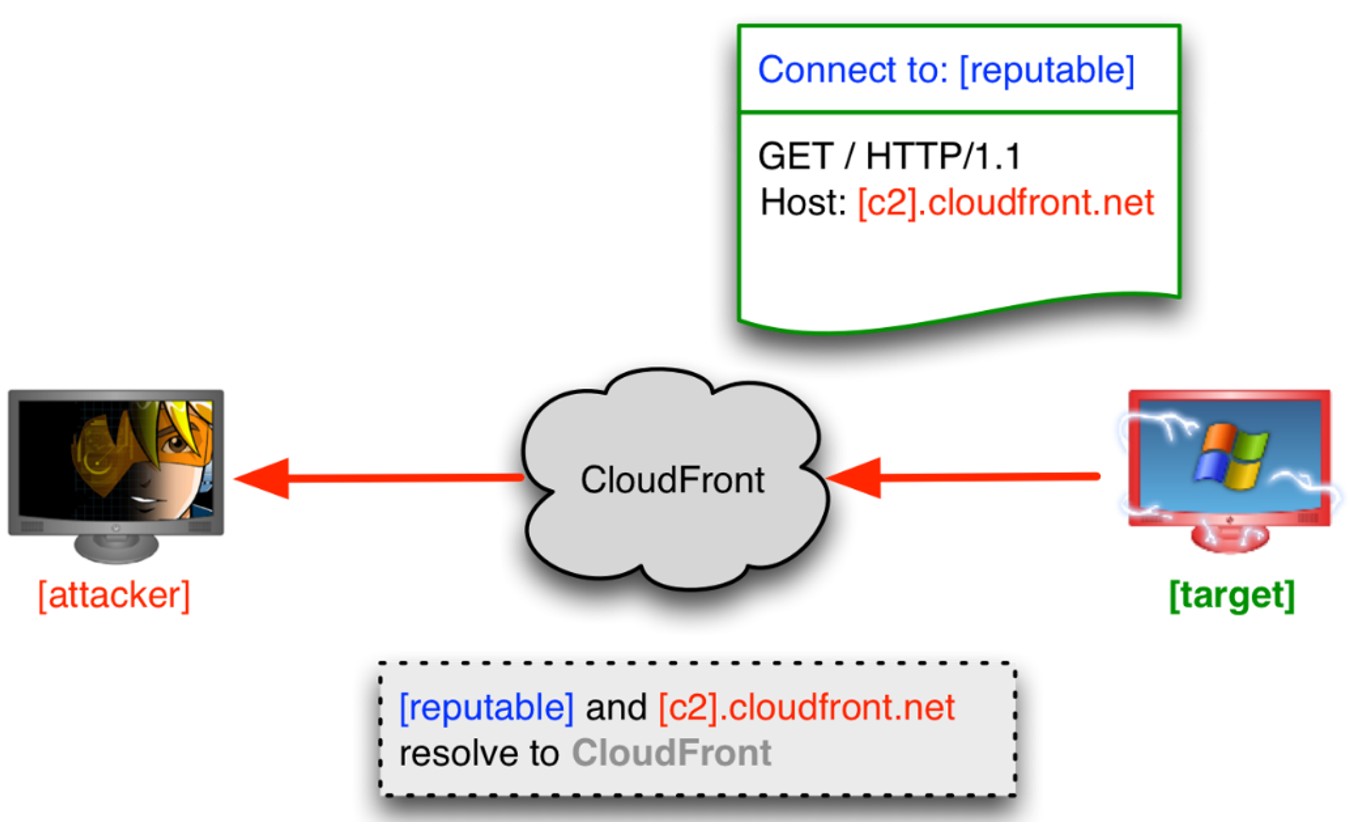
Hackers Turn the Tables: 390,000 WordPress Credentials Stolen in Supply Chain Attack
A sophisticated hacking group dubbed MUT-1244 executed a year-long campaign targeting cybercriminals and researchers through trojanized software tools. The attackers successfully stole over 390,000 WordPress credentials along with other sensitive data using deceptive GitHub repositories and infected npm packages.
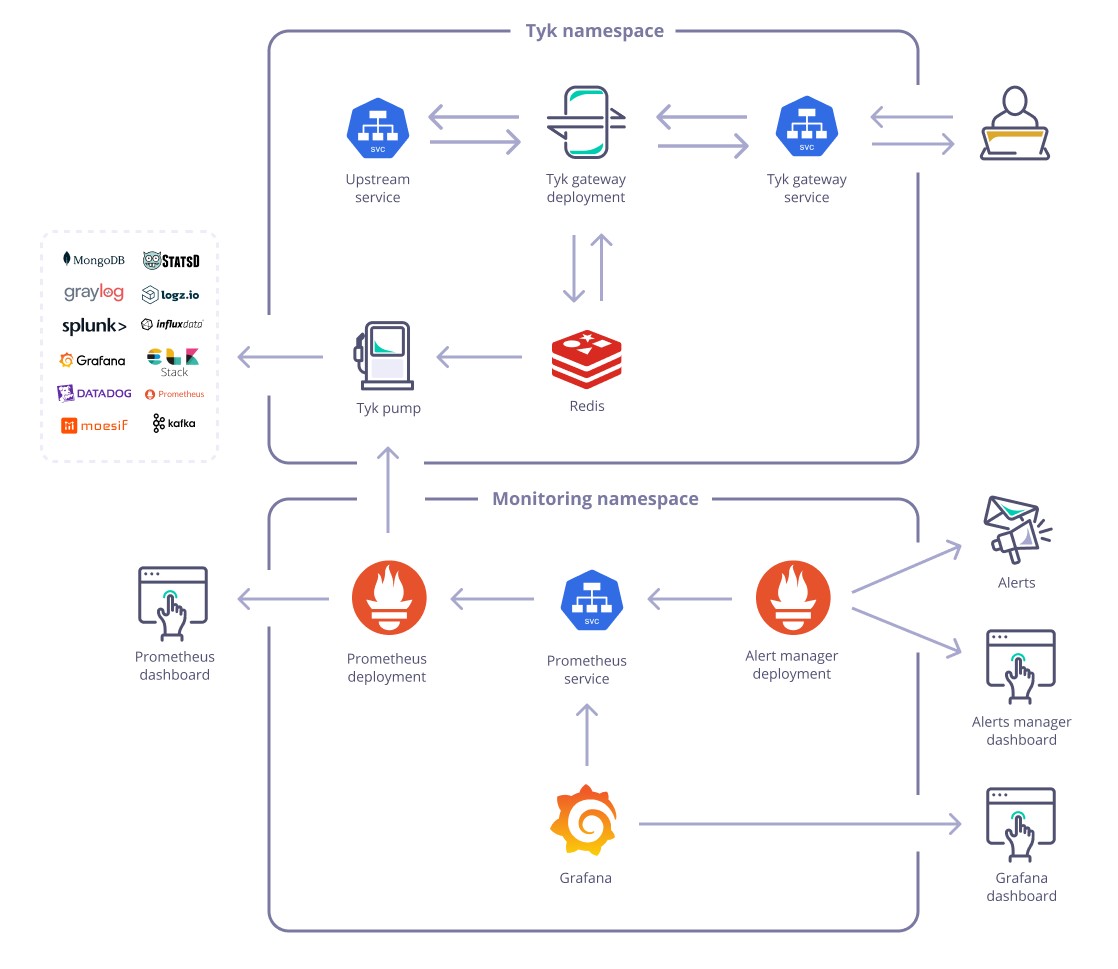
Critical Security Flaws Found in 336,000 Exposed Prometheus Monitoring Servers
Researchers discovered over 336,000 Prometheus monitoring servers and exporters exposed online, leaking sensitive data and vulnerable to DoS attacks. The investigation revealed plaintext passwords, authentication tokens, and internal API addresses were accessible, while also identifying risks from 'repojacking' vulnerabilities.