A serious security breach has been discovered in the Go Module Mirror, a Google-operated proxy service that caches open source packages for Go programming language developers. The service inadvertently served a malicious backdoored package for more than three years, security firm Socket revealed on Monday.
The compromised package, named "boltdb-go/bolt", was designed to mimic the legitimate and widely-used "boltdb/bolt" package that over 8,000 other packages rely on. This technique, known as typosquatting, takes advantage of developers who may accidentally mistype package names during installation.
The backdoored version first appeared on GitHub in November 2021. While the malicious code was eventually removed from GitHub, the Go Module Mirror had already cached the compromised version and continued serving it to unsuspecting developers for three years.
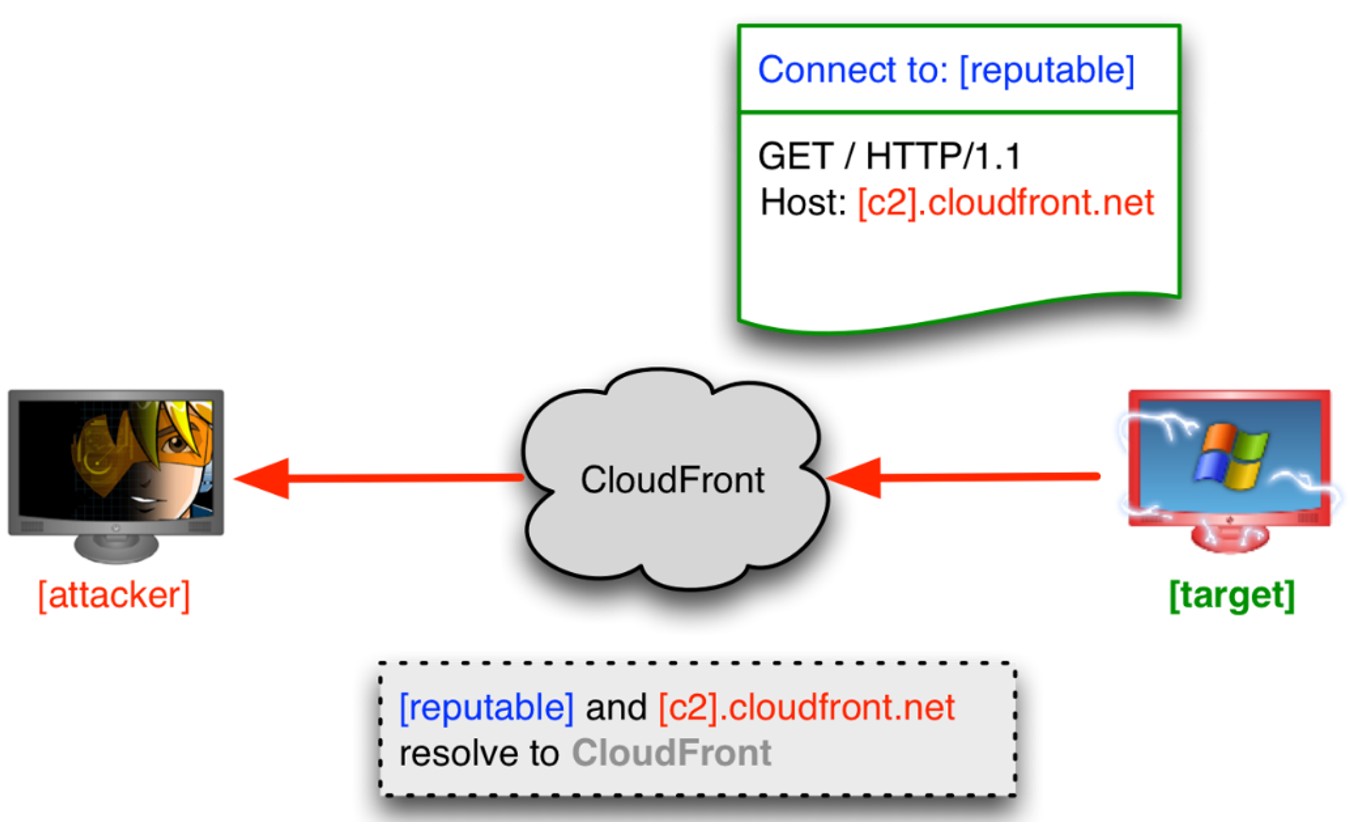
The malware was sophisticated in its approach, featuring a hidden mechanism that connected to an attacker-controlled server hosted by Hetzner Online. Once connected, the backdoor could execute remote commands, potentially compromising development environments.
The attackers employed several deceptive tactics to make their package appear legitimate, including copying the README file from the original package and taking advantage of the fact that the legitimate package had been archived, as developers often prefer active forks.
Socket researchers attempted to have the package removed twice - first on Friday and again on Monday - before it was finally taken down. The incident highlights a security weakness in the Go Module Mirror's caching system, which prioritizes performance and availability over security verification.
Google and the Go team have not yet responded to inquiries about their security verification processes for cached modules. This incident serves as a reminder for developers to carefully verify package integrity and analyze dependencies before installation in production environments.