Security researchers have discovered major vulnerabilities affecting multiple tunneling protocols that put millions of internet-connected devices at risk. The flaws could allow attackers to hijack systems and conduct anonymous attacks.
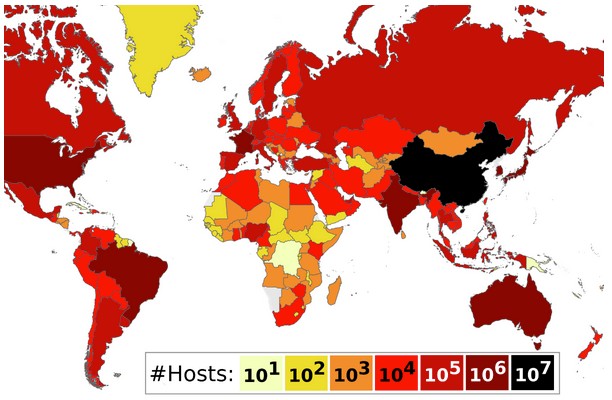
A joint study by Top10VPN and KU Leuven researcher Mathy Vanhoef revealed that approximately 4.2 million hosts are vulnerable, including VPN servers, home routers, core internet infrastructure, mobile network gateways, and content delivery networks. China, France, Japan, the United States, and Brazil are among the most impacted countries.
The security gaps exist in common tunneling protocols like IP6IP6, GRE6, 4in6, and 6in4, which are used to transfer data between disconnected networks. These protocols lack proper authentication and encryption without additional security measures like IPsec.
An attacker can exploit these flaws by sending specially crafted packets with manipulated IP headers. When a vulnerable system receives such a packet, it automatically forwards it to the intended destination while masking the attacker's true identity. This allows malicious traffic to bypass network security filters since it appears to come from a trusted host.
The discovered vulnerabilities have been assigned multiple CVE identifiers, including CVE-2024-7595, CVE-2024-7596, CVE-2025-23018, and CVE-2025-23019.
Security experts recommend implementing several protective measures:
- Using IPSec or WireGuard for authentication and encryption
- Accepting tunneling packets only from trusted sources
- Implementing traffic filtering on network devices
- Conducting deep packet inspection
- Blocking unencrypted tunneling packets
If left unaddressed, these vulnerabilities could lead to denial-of-service attacks causing network congestion and service disruptions. They may also enable man-in-the-middle attacks and unauthorized data interception.
The findings highlight the ongoing challenges in securing fundamental internet infrastructure and the need for organizations to regularly audit their network security protocols.