Ransomware attacks targeting VMware ESXi servers have intensified dramatically in 2024, with cybercriminals now demanding average ransoms of $5 million. With thousands of ESXi hosts directly exposed online, organizations face unprecedented risks to their virtualized infrastructure.
The Growing Threat Landscape
Most current ESXi-targeting ransomware stems from modified versions of the Babuk malware family, specifically engineered to bypass security measures. The threat is amplified by cybercriminals who sell initial system access to other malicious actors, creating a profitable underground marketplace.
How the Attacks Work
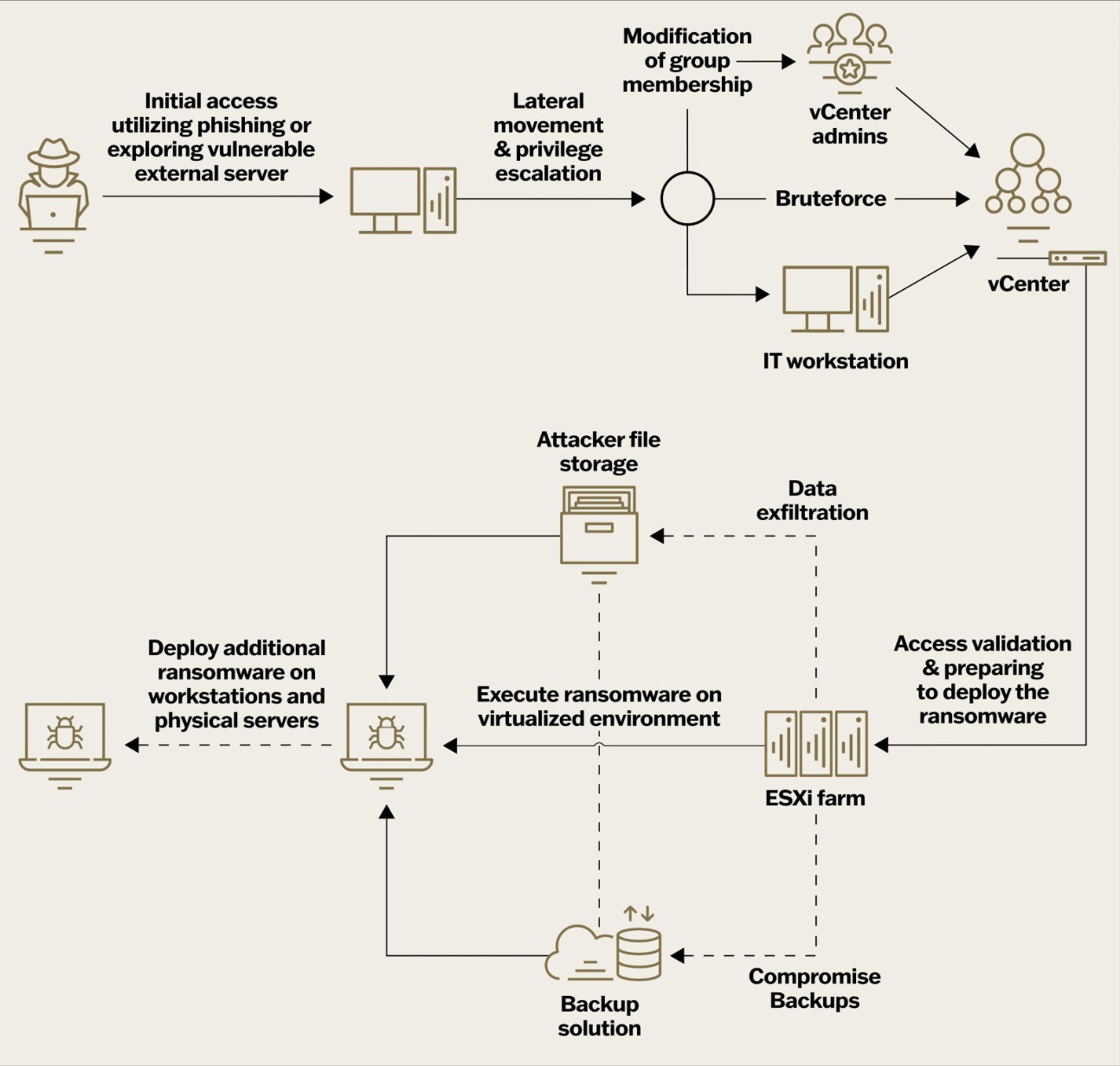
The attacks focus on compromising vCenter - the central management system for VMware infrastructure. Once attackers gain control of vCenter through its privileged "vpxuser" account, they can access and manipulate all connected ESXi hosts with root-level permissions.
The ransomware specifically targets four critical file types:
- VMDK files containing virtual machine disk data
- VMEM files handling virtual machine memory paging
- VSWP files managing memory swapping
- VMSN files storing virtual machine snapshots
The Encryption Process
Given the large size of virtualization files, attackers employ a two-pronged encryption strategy:
- Fast symmetric encryption (like AES) to scramble the actual data
- Slower asymmetric encryption to protect the encryption keys themselves
Protection Strategies
Organizations can defend against these threats through:
- Regular updates of VMware vCenter Server Appliance
- Implementation of multi-factor authentication
- Deployment of specialized detection tools
- Strategic network segmentation
- Ongoing security testing and assessment
The rise in ESXi ransomware attacks highlights the need for organizations to strengthen their virtual infrastructure security and maintain vigilant monitoring of their systems.