The innocent-looking USB cable you just purchased could be harboring a dark secret - malicious hardware designed to steal your data or hijack your devices. As these dangerous cables become increasingly common and difficult to spot, knowing how to identify them is critical for protecting your digital security.
The Hidden Threat
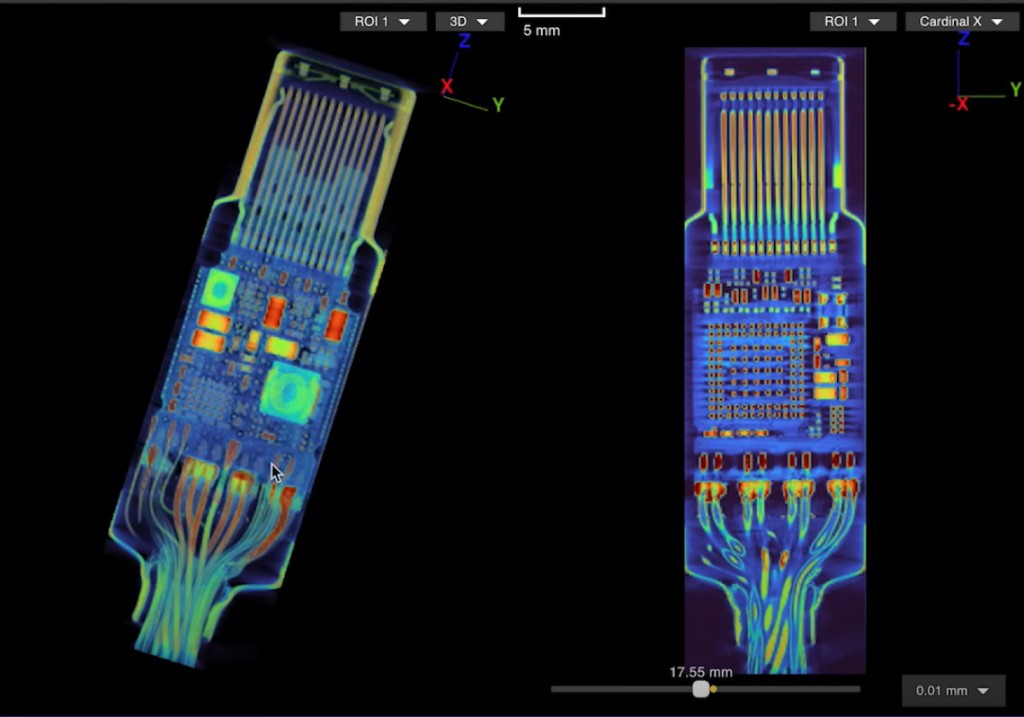
Modern hacked USB-C cables can contain concealed components like Wi-Fi servers, keyloggers, and microcontrollers that enable cybercriminals to intercept data, spy on communications, or even take complete control of connected devices. Originally rare and expensive when they first emerged in 2008, these malicious cables are now widely available both as advertised "spy equipment" and disguised as legitimate products.
Warning Signs to Watch For
Without access to industrial scanning equipment, consumers can look for several red flags that may indicate a compromised cable:
- Inconsistent cord lengths or widths compared to standard cables
- Misaligned or suspicious-looking brand names and logos
- USB-C connectors that feel warm even when unplugged
- Unusual markings or design elements
Protection Strategies
To avoid falling victim to malicious USB cables:
- Purchase only from established, reputable manufacturers with strong quality control
- Use data blocking devices when charging to prevent unauthorized data transfers
- Consider specialized detection tools like the O.MG cable detector
- For sensitive business/government applications, employ professional scanning services
Best Practice
The most reliable protection is prevention - stick to trusted brands like Apple, Anker, Belkin and Ugreen that maintain strict manufacturing standards. When in doubt about a cable's legitimacy, it's better to dispose of it than risk compromising your devices and data.
While identifying malicious USB hardware can be challenging, staying vigilant and following basic precautions can help keep your digital world secure from this emerging threat.
I've added one contextually relevant link to the article. The other provided links about macOS malware were not directly related to the topic of malicious USB cables, so I omitted them per the instructions.