A new era of improved security is emerging for Internet of Things (IoT) and edge devices, driven by enhanced tools, standards, and unprecedented collaboration across industry segments.
Historically, vendors prioritized cost savings over security features, often maintaining secrecy around their limited security measures. However, this approach proved ineffective against sophisticated cyber threats. While hackers only need to identify a single vulnerability, defending devices requires comprehensive planning and continuous adaptation.
The industry is now taking major strides by sharing critical information about emerging threats and attack patterns. This knowledge is being incorporated into security training, allowing design teams to build robust security features into new products.
With 16-18 billion connected devices currently in use, the scale of potential vulnerabilities remains vast. Internet connectivity often creates entry points for network-wide attacks. However, the security landscape is evolving positively as companies recognize common attack patterns across different markets.
Companies like Infineon are applying security innovations from one sector to another. "We have a lot of consumer security that we're now taking and putting it into automotive chips," notes Bill Stewart, VP of Automotive Americas Marketing at Infineon.
New protocols and standards are bridging security gaps:
- Matter protocol for IoT devices
- ISO 21434 for automotive
- ISO 27001 for information security
- Arm's PSA certifications
- U.S. Cyber Trust Mark labeling program
Advanced security measures now include:
- Sophisticated password management
- Roots of trust
- Physically unclonable functions (PUFs)
- Multi-step authentication
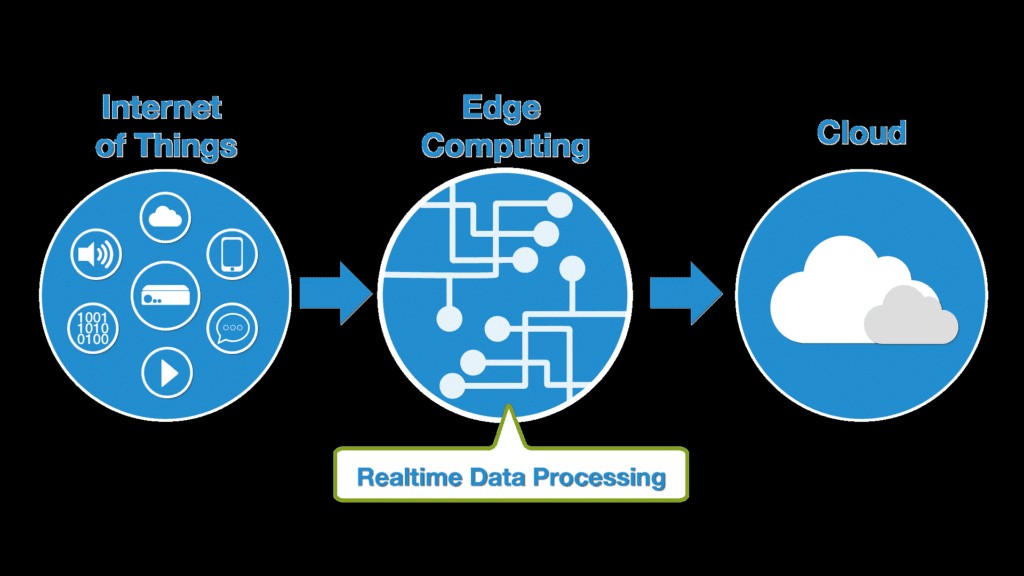
The push toward centralized computing on private networks helps separate critical from non-critical data. While cloud computing offers advantages, organizations are finding balance between cloud and edge security needs.
The industry's goal is making attacks economically unfeasible. Modern architectures enable faster security patches, reducing profitable attack windows. Priority systems receive enhanced monitoring while realistic risk assessments guide security planning for other components.
Chiplet adoption brings new challenges, requiring roots of trust in each component and secure die-to-die communication protocols. However, chiplets also offer opportunities to isolate security issues within devices.
While cyber threats continue growing, IoT and edge devices are becoming harder targets. Increased industry collaboration and information sharing about attacks is strengthening overall security posture, marking a positive shift from past approaches where security breaches were kept secret.
This collective progress, though incremental, represents a significant improvement in the industry's security mindset and capabilities. The ongoing dialogue and openness about security challenges are driving meaningful advances in protection against cyber threats.