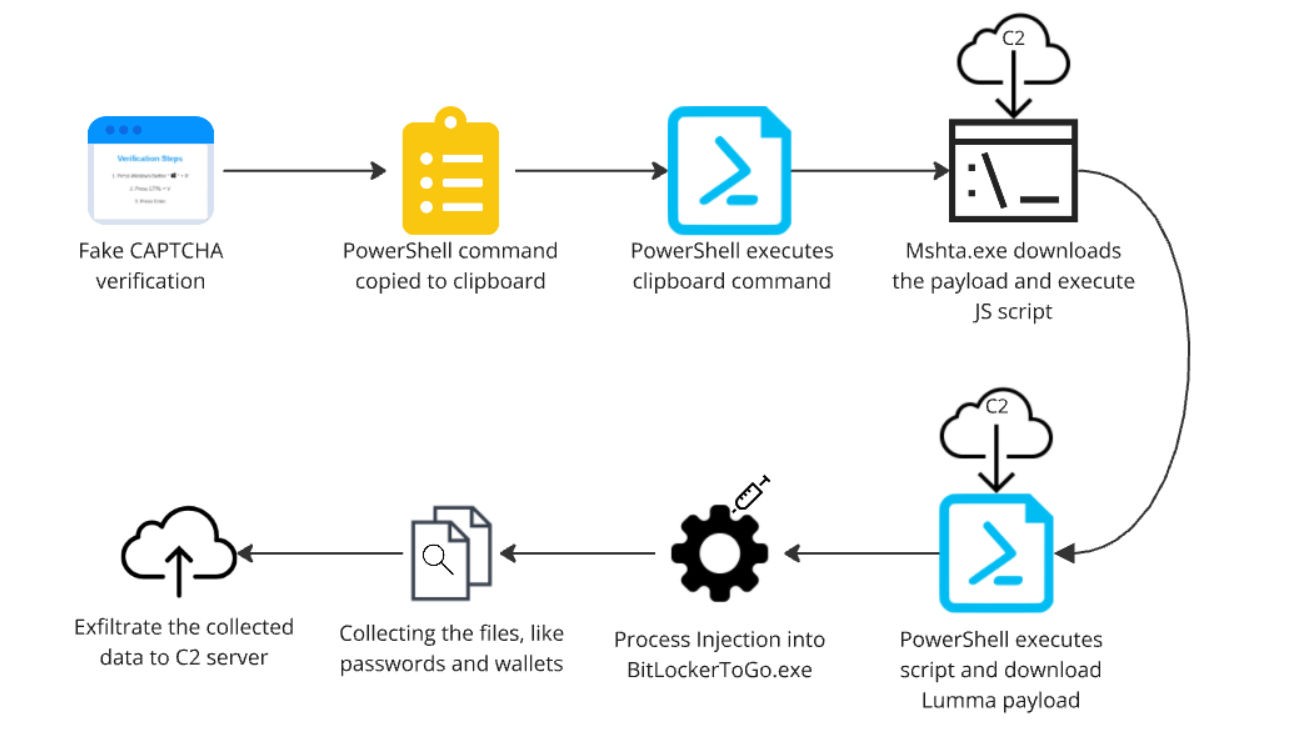
Security researchers have uncovered a major malware campaign that targets users through fake CAPTCHA verification pages to distribute the dangerous Lumma information-stealing malware. The attack has reportedly reached millions of users through compromised online advertising networks.
According to findings from Guardio Labs and Infoblox, cybercriminals are exploiting the digital advertising infrastructure to show malicious CAPTCHA pages to visitors of legitimate websites. When users attempt to complete what appears to be a standard verification prompt, malware is secretly installed on their systems.
The installed Lumma malware targets sensitive data including social media passwords, banking credentials, and personal files stored on infected devices.
The campaign's massive reach involves over 1 million daily ad impressions spread across more than 3,000 websites. The attackers used sophisticated methods to hide their malicious intent, including ad tracking services and traffic distribution systems that help evade detection.
"This fake CAPTCHA scheme reveals concerning vulnerabilities in internet advertising," noted researchers. The fragmented nature of online advertising - with multiple parties handling ad placement, tracking, and hosting - creates gaps that criminals can exploit.
After being notified, advertising networks took action by shutting down hundreds of accounts connected to the campaign. However, experts warn that more preventive security measures are needed across the advertising ecosystem to protect users from similar threats.
The discovery highlights how cybercriminals continue finding new ways to abuse legitimate web infrastructure for distributing malware. Users are advised to be cautious of unexpected CAPTCHA prompts and to maintain updated security software.