Security researchers have detected an extensive scanning operation targeting Palo Alto Networks GlobalProtect VPN portals, with nearly 24,000 unique IP addresses attempting to access these systems over the past month.
According to cybersecurity firm GreyNoise, the scanning activity began on March 17, 2025, maintaining a rate of approximately 20,000 unique IP addresses per day before declining on March 26. The campaign primarily focused on systems in the United States, with additional targets identified in the United Kingdom, Ireland, Russia, and Singapore.
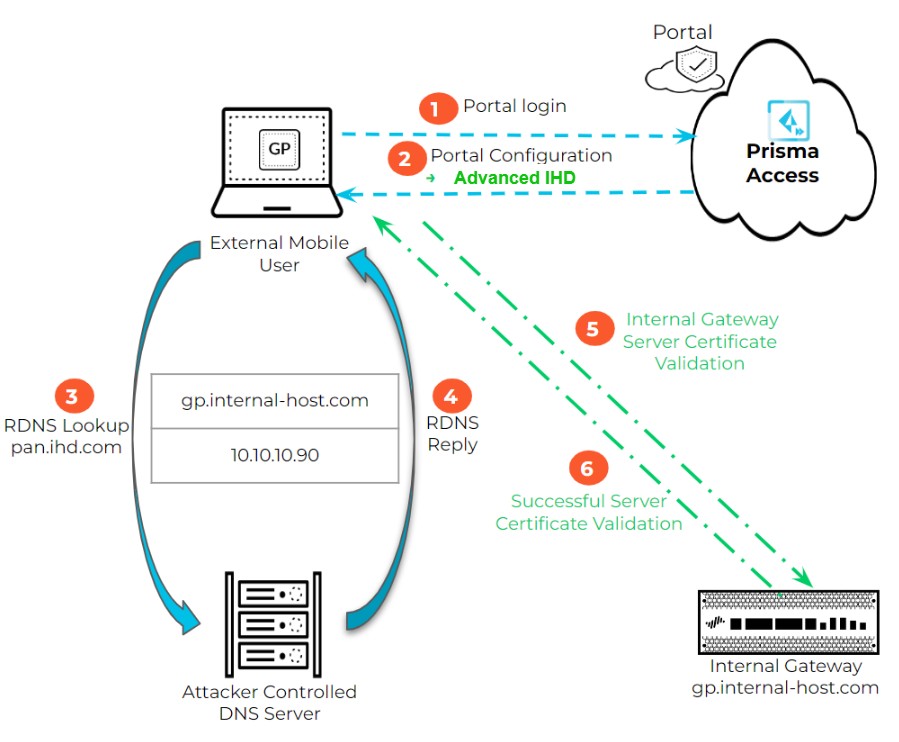
The GlobalProtect portal serves as a critical component of Palo Alto's enterprise VPN solution, enabling remote user authentication and secure access to corporate networks. Analysis by GreyNoise revealed that the scanning attempts originated from a single login scanner tool, identified through three distinct digital fingerprints.
While most of the observed IP addresses (23,800) were classified as suspicious, 154 IPs demonstrated clearly malicious behavior. The researchers also noted a brief spike in crawler activity on March 26, specifically probing for GlobalProtect components potentially vulnerable to command injection attacks.
Bob Rudis, VP of Data Science at GreyNoise, noted that similar patterns of reconnaissance activity have historically preceded the discovery of new vulnerabilities by 2-4 weeks. "Over the past 18 to 24 months, we've observed consistent targeting of older vulnerabilities against specific technologies," Rudis explained.
Organizations using Palo Alto Networks systems are advised to review their March logs and conduct thorough security assessments to identify potential compromises. The coordinated nature of this campaign suggests a systematic approach to testing network defenses, possibly laying groundwork for future exploitation attempts.