A sophisticated scam campaign masquerading as the BianLian ransomware group has emerged, targeting corporate executives through an unusual method - physical mail delivery.
Security firm GRIT reports that in early March 2025, multiple organizations received suspicious letters from US addresses claiming their networks were compromised. The letters, which mimic legitimate ransomware extortion tactics, demand ransoms between $250,000 to $350,000 in Bitcoin within 10 days to prevent alleged stolen data from being leaked.
While the letters include authentic-looking elements like Bitcoin wallet QR codes and links to BianLian's dark web sites, several red flags point to their fraudulent nature. Most notably, legitimate ransomware groups never communicate ransom demands via postal mail, preferring digital channels to prove network compromise.
The letters' writing style also raises suspicion, featuring flawless English and complex sentence structures unlike BianLian's typical communications. Additionally, the notes lack standard negotiation contact details, with perpetrators claiming they "no longer negotiate" - an unusual stance for real ransomware operators.
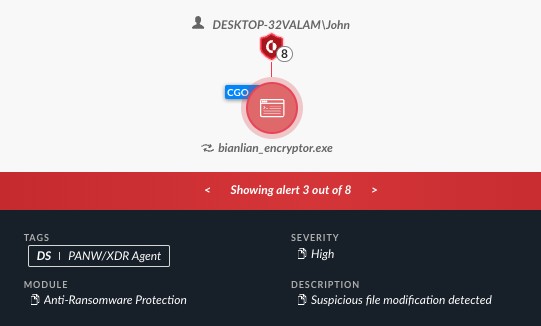
Most tellingly, organizations receiving these letters show no signs of actual network intrusion or ransomware activity. The Bitcoin wallets listed are newly created with no connection to known cybercrime groups.
Based on these inconsistencies and the letters' US origin, GRIT concludes this is likely an opportunistic scam attempting to exploit executives' fears of ransomware attacks. Organizations are advised to verify any ransom demands through proper security channels rather than rushing to pay unsubstantiated claims.
The emergence of this postal scam highlights how cybercriminals continue finding creative ways to prey on ransomware anxiety, even through traditional mail fraud tactics.