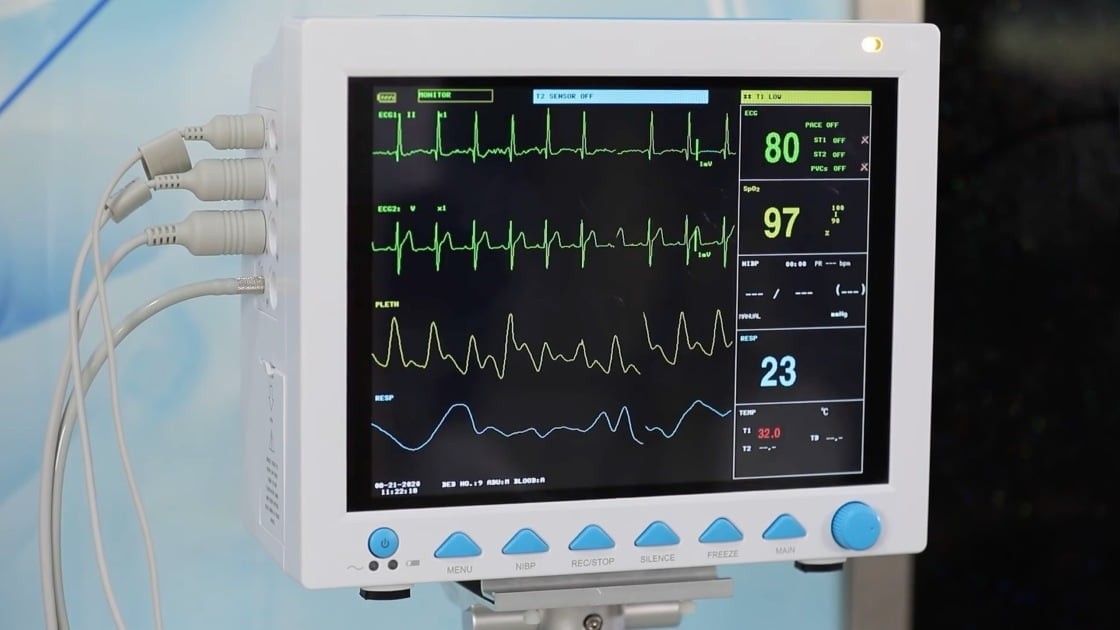
Recent alerts from U.S. regulators raised concerns about potential backdoors in CONTEC CMS8000 patient monitors, but new research reveals a more nuanced security situation.
On January 30th, both the Cybersecurity Infrastructure & Security Agency (CISA) and the Food and Drug Administration (FDA) issued warnings about the Chinese-manufactured CONTEC CMS8000 patient monitors, suggesting they contained hidden backdoor functionality communicating with servers in China.
However, detailed analysis by security researchers indicates the issue stems from poor security design rather than intentional malicious backdoors. The IP addresses flagged as suspicious (202.114.4.119 and 202.114.4.120) are actually documented in the manufacturer's manuals as default configurations for the device's Central Management System (CMS) and HL7 medical data sharing.
"While this doesn't appear to be a deliberate backdoor, it remains a serious security vulnerability," explains the research team. "Using public internet IP addresses for sensitive medical device functions creates major risks for healthcare providers."
The key security issues identified include:
- Hardcoded public IP addresses that could enable patient data leakage
- An insecure firmware update mechanism using NFS network shares
- Unencrypted transmission of patient vital signs and medical data
- Potential for remote code execution if exploited
The researchers demonstrated these vulnerabilities by successfully executing malicious code on a test device, showing how attackers could potentially manipulate vital sign readings or disable monitors entirely.
Healthcare organizations using these devices are advised to:
- Block all network traffic to the 202.114.4.0/24 subnet
- Modify default CMS IP configurations where possible
- Implement network segmentation to contain device communications
- Consider replacing devices with more secure alternatives
While not as alarming as an intentional backdoor, the security flaws in these widely-used patient monitors still pose risks that healthcare providers must address through careful network controls and security measures.
The findings highlight the broader challenges of medical device security and the need for manufacturers to implement more robust security practices, especially for devices handling sensitive patient data.