Top U.S. Security Officials' Private Data Exposed in Major Privacy Breach
Personal information including phone numbers, emails and passwords of high-ranking national security officials has been found exposed online through public databases and leaks. The breach raises serious concerns about data protection and potential security risks for sensitive government operations.
DollyWay Malware Campaign: The Eight-Year Evolution of a WordPress Threat
A sophisticated malware operation called DollyWay has compromised over 20,000 WordPress sites since 2016, redirecting millions of visitors to fraudulent pages. The campaign's third iteration employs advanced techniques like cryptographic signing and multiple injection methods to maintain persistence.
Critical Vulnerabilities in mySCADA myPRO Put Industrial Control Systems at Risk
Two severe security flaws discovered in mySCADA myPRO industrial control system could allow attackers to seize control of critical infrastructure. The vulnerabilities, rated 9.3 out of 10 in severity, enable command injection attacks through inadequate input validation.
Former NFL Coach Charged in Massive Student-Athlete Data Breach and Identity Theft Scheme
Matt Weiss, former NFL and Michigan assistant coach, faces federal charges for allegedly hacking into thousands of college athletes' accounts to obtain private content. The indictment details how he infiltrated databases across 100+ universities, accessing personal data of over 150,000 athletes between 2015-2023.
Kali Linux 2025.1a Debuts with Sleek Visual Overhaul and Enhanced Mobile Testing
The latest Kali Linux release brings a modern visual refresh across desktop environments, with KDE Plasma 6.2 and Xfce 4.20 updates. Notable improvements include expanded Raspberry Pi 5 support and advanced mobile penetration testing capabilities through Kali NetHunter.
Telegram CEO Durov Returns to Dubai Amid French Criminal Probe
Pavel Durov, Telegram's CEO, has temporarily left France for Dubai while facing criminal charges over alleged platform moderation failures. The investigation continues as Telegram implements new content safety measures, though Durov maintains his innocence.
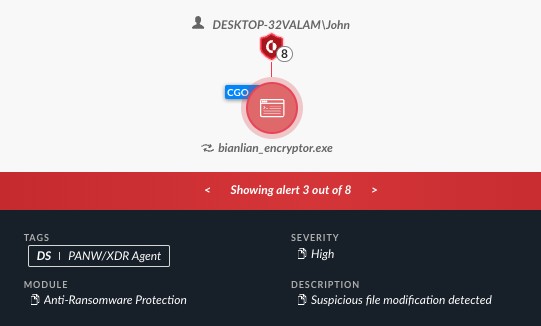
Scammers Impersonate BianLian Ransomware Group in Mail-Based Extortion Scheme
A sophisticated scam operation is targeting executives with fake ransomware demands delivered via physical mail, impersonating the notorious BianLian group. The fraudulent letters demand large Bitcoin ransoms while displaying key inconsistencies that reveal their opportunistic nature.
12,000 API Keys Found Exposed in LLM Training Data Raising Security Concerns
Security researchers discovered thousands of hardcoded credentials within Common Crawl dataset used to train large language models, posing significant cybersecurity risks. The exposed API keys and passwords, many reused across multiple sites, could enable malicious actors to exploit AI systems for unauthorized access and harmful content generation.
Chinese State-Backed Hackers Breach Belgian Intelligence Agency Through Email Security Flaw
Chinese hackers infiltrated Belgium's State Security Service over two years, accessing 10% of staff emails through a Barracuda system vulnerability. While classified data remained protected, the breach exposed sensitive HR information during a critical recruitment period.
China's Cyber Offensive: State-Backed Hacking Groups Show Unprecedented Sophistication
Chinese state-sponsored cyber operations have surged 150% in 2024, with specialized groups like Salt Typhoon targeting critical infrastructure and telecom networks. The dramatic evolution in capabilities and stealth tactics signals China's strategic focus on maintaining persistent network access for potential military advantages.