T-Mobile Hit by Data Breach in Latest Attack on Telecom Giants
T-Mobile confirms unauthorized access to its systems in a recent cybersecurity incident, marking the latest in a series of attacks targeting major telecommunications providers. The company is working with security experts and law enforcement while advising customers to change passwords and enable two-factor authentication.
Massive Data Breach at Set Forth Exposes 1.5 Million Customers' Personal Information
Set Forth, a major American debt services firm, suffered a significant data breach compromising sensitive data of 1.5 million customers and their families. The company discovered unauthorized system access in May 2024, leading to the theft of personal information including social security numbers.
Major Cyberattack Paralyzes Payment Systems Across Israel
A widespread cyberattack disrupted payment processing networks throughout Israel, forcing businesses to halt card transactions and accept only cash. The incident exposed vulnerabilities in critical payment infrastructure while cybersecurity teams worked to restore services and implement additional protections.
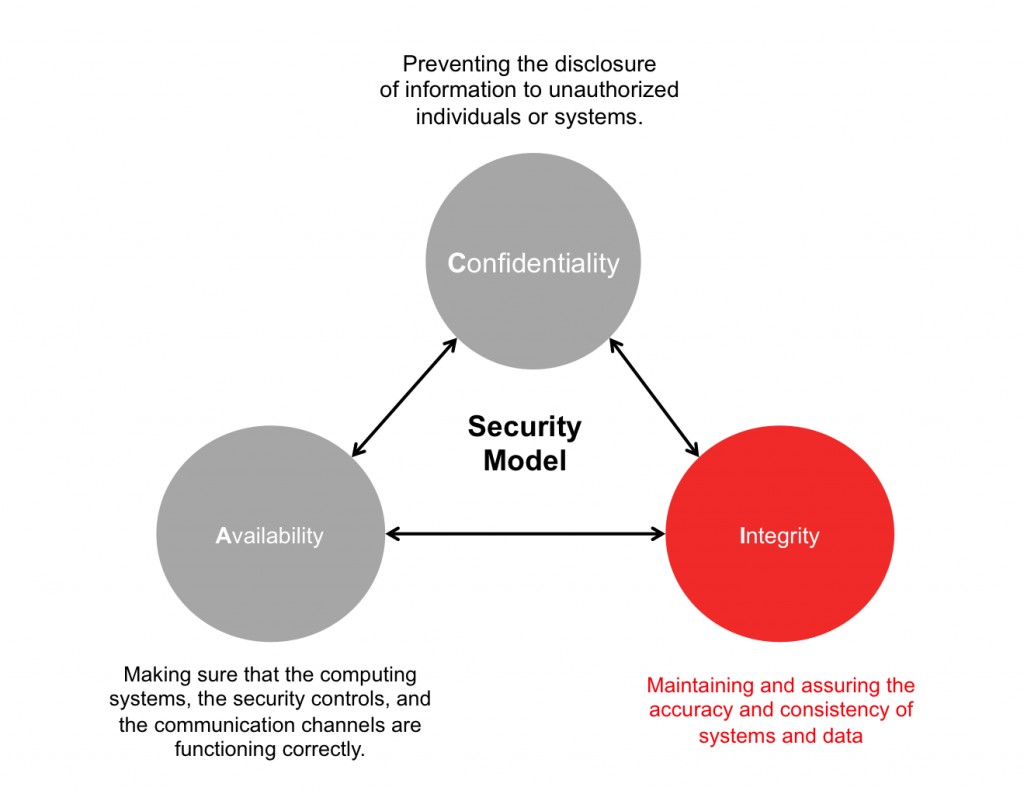
The Hidden Danger of Useless Security Controls: Wasting Resources and Undermining Cybersecurity
Many organizations implement ineffective security measures that waste resources and potentially make systems less secure. Learn how to identify and eliminate these useless controls to focus on genuine cybersecurity challenges.
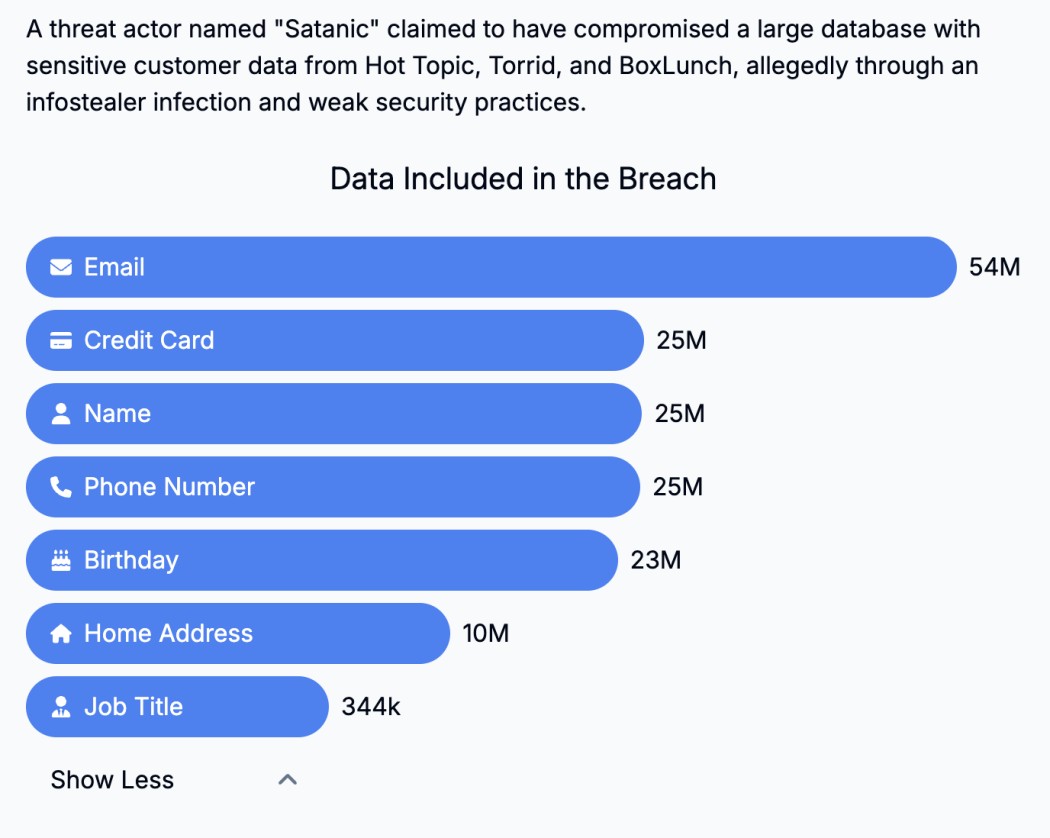
57 Million Hot Topic Customers Alerted to Data Breach by Have I Been Pwned
Have I Been Pwned notifies 57 million individuals of a major data breach at Hot Topic, a popular retail chain. Affected customers are urged to take immediate action to protect their personal information.
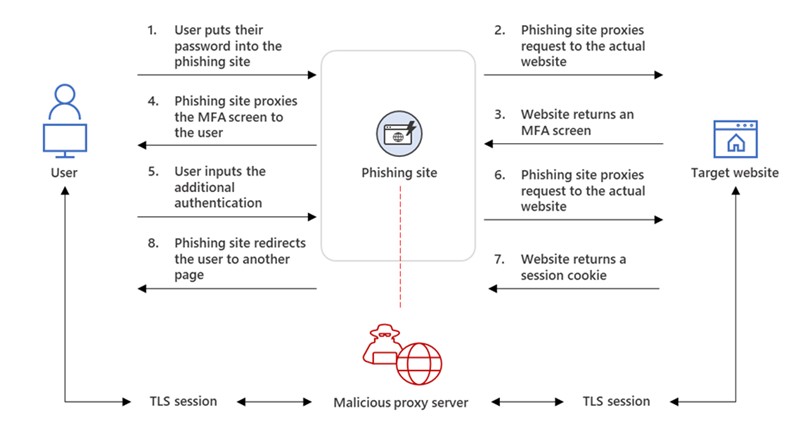
Critical Flaw in Microsoft Bookings Exposes Users to Account Hijacking and Impersonation
A severe vulnerability in Microsoft Bookings allows unauthorized access and key personnel impersonation, raising cybersecurity concerns. Users are advised to implement additional security measures while Microsoft works on a fix.
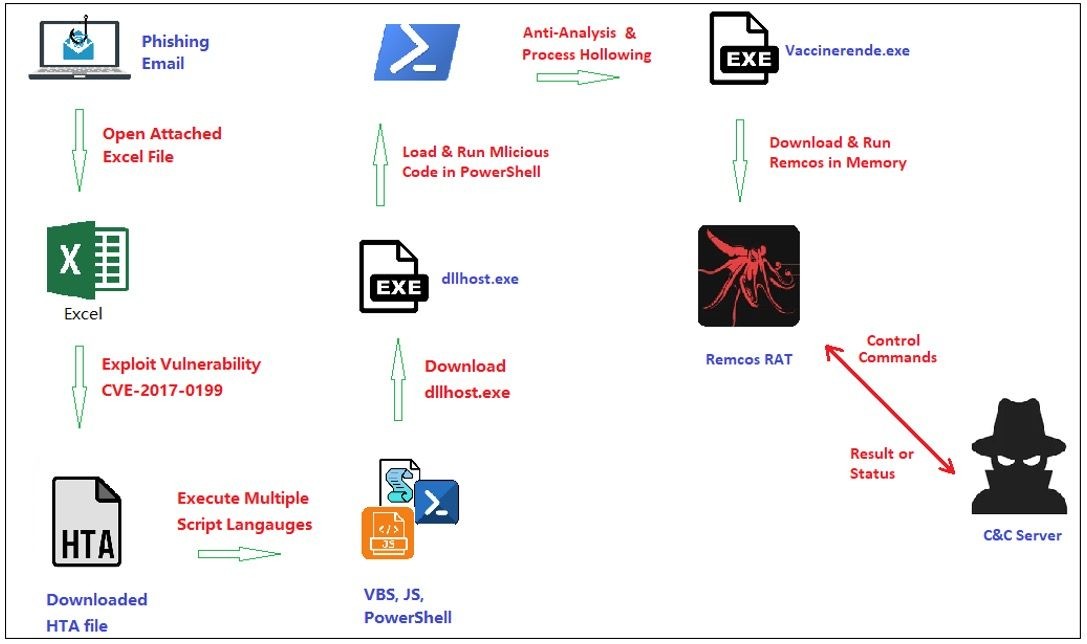
Stealthy New Remcos RAT Variant Evades Detection with Fileless Techniques
Security researchers uncover a sophisticated new version of the Remcos remote access trojan using advanced evasion methods. This fileless malware variant exploits vulnerabilities and leverages legitimate processes to avoid detection while providing attackers extensive remote control capabilities.
The Rising Threat of AI Deepfakes: Navigating Cybersecurity Challenges in a Synthetic World
AI-powered deepfakes pose significant risks to cybersecurity, enabling sophisticated identity theft and social engineering attacks. As the technology advances, combating these threats requires a multi-faceted approach involving detection algorithms, media authentication, and increased public awareness.