India Moves to Block Proton Mail Over Privacy and Security Concerns
Indian court orders nationwide ban on encrypted email service Proton Mail following complaints of harassment and misuse. The controversial decision highlights growing tensions between privacy-focused technology and government regulation of digital communications.
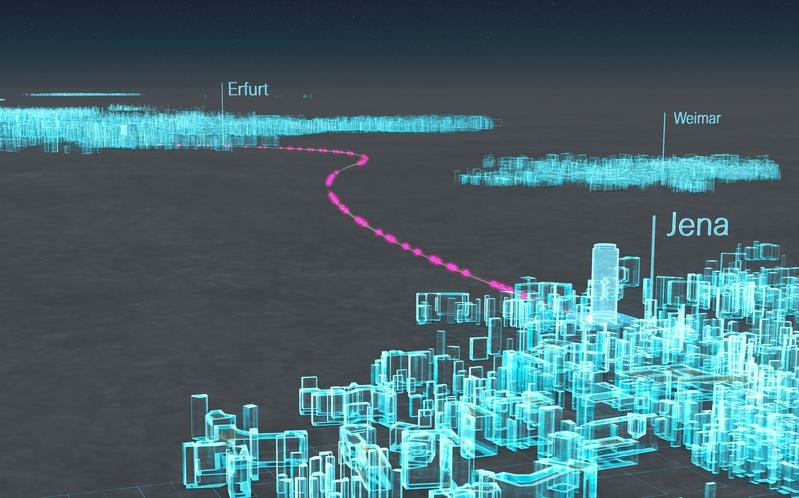
Germany Achieves Quantum Communication Breakthrough Using Standard Fiber Networks
Researchers successfully transmitted quantum-encrypted messages across 254km of commercial fiber optic cables in Germany without specialized equipment. This breakthrough demonstrates that quantum networks can be implemented cost-effectively using existing telecommunications infrastructure.
U.S. Army Expands Enterprise Wickr Platform to Enhance Secure Military Communications
The U.S. Army is broadening access to its Enterprise Wickr encrypted messaging system to combat unauthorized app usage and strengthen military communications security. The expansion follows successful trials demonstrating enhanced integration capabilities between soldiers, foreign militaries, and partners in various mission scenarios.
VanHelsing: Cross-Platform Ransomware Service Targets Global Organizations
A sophisticated new ransomware-as-a-service called VanHelsing has emerged, targeting multiple operating systems with advanced encryption capabilities. The malware has already claimed victims across the US and France, with affiliates receiving up to 80% of ransom payments that can reach $500,000.
Signal Threatens Swedish Withdrawal Over Proposed Surveillance Law
Signal CEO Meredith Whittaker firmly opposes Sweden's proposed law requiring messaging apps to store user communications for law enforcement access. The encrypted messaging service vows to exit the Swedish market rather than compromise its security architecture with backdoors.
Google Cloud Pioneers Quantum-Safe Digital Signatures to Combat Future Encryption Threats
Google Cloud introduces quantum-resistant digital signatures in Cloud KMS, implementing NIST's post-quantum cryptography standards through ML-DSA-65 and SLH-DSA-SHA2-128S algorithms. This proactive measure helps organizations protect against future quantum computing threats while maintaining robust encryption standards.
Inside Sky Global: How an Encrypted Phone Network Became a Criminal Enterprise
A Vancouver tech company marketed ultra-secure phones for privacy but investigations revealed their devices were predominantly used by organized crime networks worldwide. After European authorities cracked Sky ECC's encryption in 2021, evidence showed the company's distribution channels had deep criminal ties while compliance efforts were largely superficial.
Essential Smartphone Security Guide for Protesters: Protecting Your Digital Rights
A comprehensive guide to securing smartphones during protests, covering crucial pre-event preparation, real-time best practices, and post-demonstration data protection. Learn how to safeguard your device, privacy, and fellow protesters while documenting important moments.
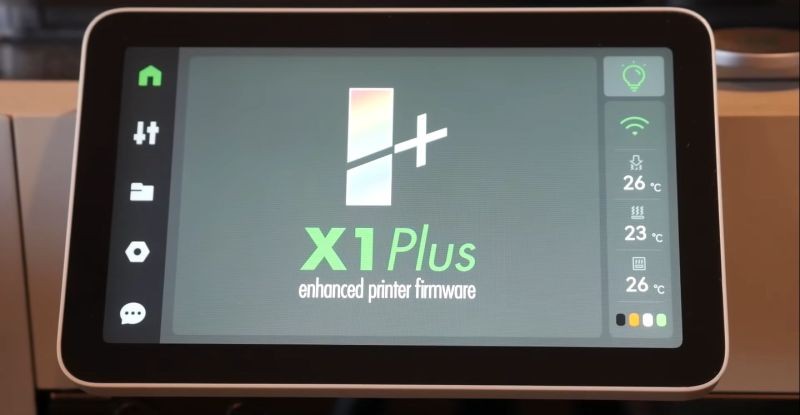
Critical Security Flaws Found in Bambu Connect 3D Printer Software
Security researchers have exposed significant vulnerabilities in Bambu Connect's 3D printer control application, revealing weak encryption and easily bypassed security measures. The findings demonstrate how malicious actors could potentially access sensitive data through reverse engineering of the Electron-based software.
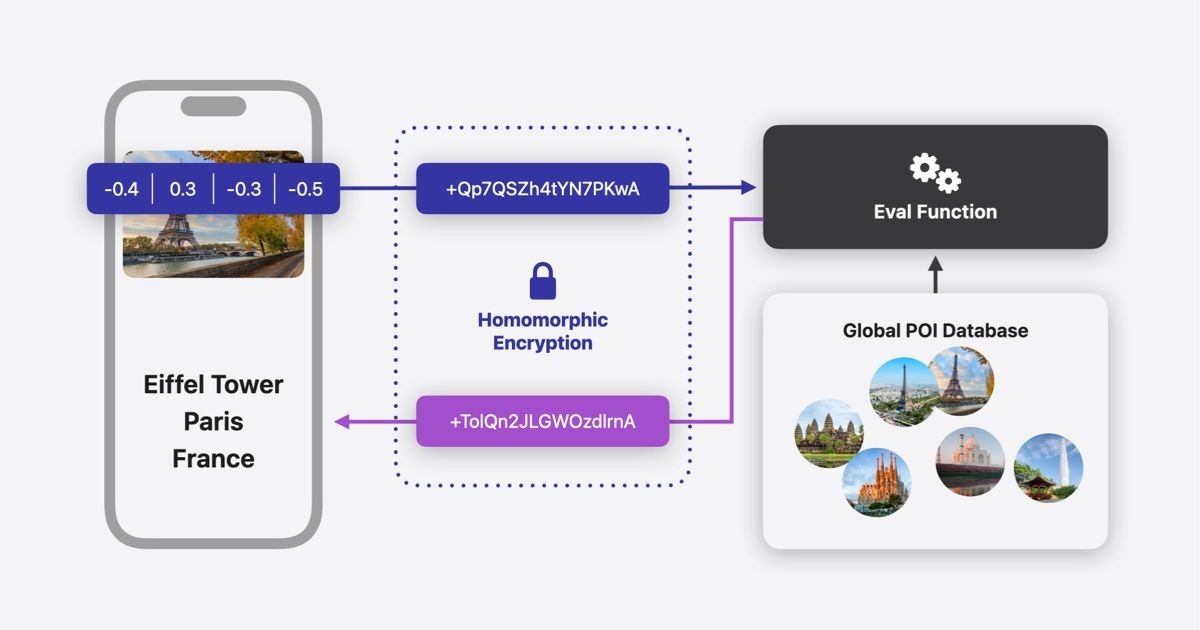
Apple Revolutionizes Photo Privacy with Homomorphic Encryption in iOS18
Apple introduces groundbreaking privacy-preserving search in iOS 18's Photos app using homomorphic encryption, allowing users to search images without exposing data to servers. The innovative 'Wally' system processes encrypted queries while maintaining complete user privacy.